There might be $500 billion wiped away from the total cryptocurrency market cap, but now news is breaking that Ledger hardware wallets aren't very safe at all.
Ledger has posted on their Twitter account reminding users that they should "always verify [their] receiv[ing] address" by checking the "monitor screen" at the bottom of the transaction request form.
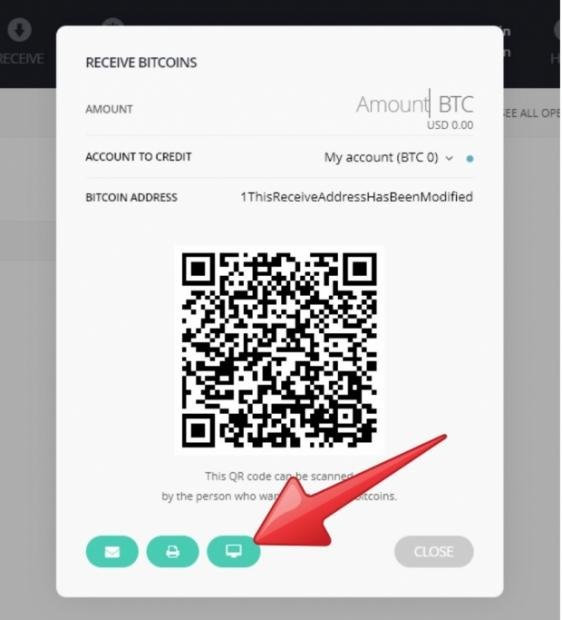
DocDroid posted a vulnerability report a few days ago, stating that Ledger hardware wallets have a major flat that lets attackers infect your crypto wallet with malware, and then trick users to send crypto to the hackers. The report stated: "Ledger wallets generate the displayed receive address using JavaScript code running on the host machine. This means that a malware can simply replace the code responsible for generating the receive address with its own address, causing all future deposits to be sent to the attacker".
There's a major problem here is that Ledger's design is inherently flawed, as the hardware wallet requires new addresses to be generated constantly, which doesn't give owners an option to "verify the integrity of the receive address". This could lead some users to thinking that a hackers' receiving address is fine, and then transfer their crypto to them.
DocDroid's report continues, saying that all Ledger software is easily exploited and can be modified by simple unprivliged malware. This means that users can get into the system, without the requirement of administrative rights. Wow.
Ledger's wallets can't check for integrity in their current state, which means they have no anti-tampering protection from these holes. DocDroid goes for the throat, saying that Ledger wallets are so badly designed that pre-infected devices could hijack users' first-ever transaction, which is just awful.
But don't worry, because Ledger replied to the report where they said on Twitter that the issue "cannot be solved in the absolute". The company continued: "A malware can always change what you see on your computer screen. The only solution is prevention and building an UX to make the user check on its device. On device verification feature has been added [six] month ago already".
More Crypto News/Content:
Russian scientists busted mining crypto in NUCLEAR facility
6 x GPU packs now on sale for miners, GTX 1060s or GTX 1080s
NVIDIA says cryptocurrency demand 'exceeded expectations'
NVIDIA: 'we are 10x bigger than our GPU competitor'
GPU prices slightly better, GTX 1080 Ti is now 'only' $1100
Ledger owner? Your cryptocurrency can be easily STOLEN
$4 trillion wiped off stock market, tech stocks are HURTING
US credit card companies block cryptocurrency purchases
Samsung announces it's making cryptocurrency mining chips
NVIDIA Tesla V100: $8000 card is the BEST to mine Ethereum
Ripple (XRP) sets a new all-time record price of $3.17
Ethereum closes in on $1000, momentum isn't stopping
Ethereum reaches new record all-time high price of $870
Ripple (XRP) value blows up, bypasses Ethereum's market cap
Crypto expert kidnapped, had to pay $1 million BTC ransom
UnikoinGold is now available on Bittrex
Bitcoin could be worth $0, according to Morgan Stanley
Facebook Messenger malware mines Monero on users' PCs
Using 'blockchain' in new name, company shares rise 500%
MiningSky 8-GPU Mining Rig V1 Review
French dominatrix pimps clients out in 'Crypto Slave Farm'
North Korea hijacking cryptocurrency industry workers