And so the cyber pandemic continues, with Samsung now hacked by the same team that stole over 1TB of confidential data from NVIDIA.
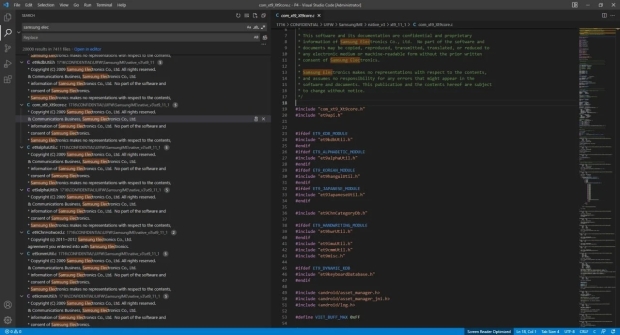
Samsung has been hacked by Lapsus$ with over 190GB of confidential information -- including source code for Samsung's Trusted Applet for secure operations -- you know, hardware cryptography, and more. Not only that, but the hackers have reportedly gotten their hands-on "algorithms for all biometric unlock operations", the "bootloader source code for all recent Samsung devices", and even "confidential source from Qualcomm".
The hackers made the 190GB of downloaded information from Samsung's servers as a torrent, with the hacking group saying that it would deploy additional servers to get the download speed up higher.
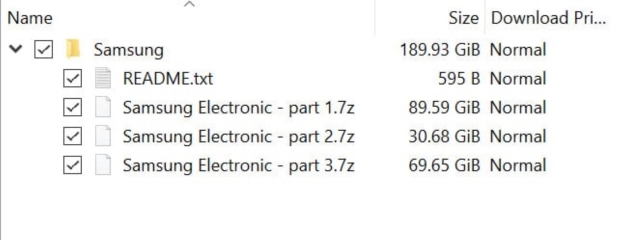
Inside of the 190GB torrent is a brief description of what Lapsus$ has inside of the three archives that it hacked from Samsung:
- Part 1 contains a dump of source code and related data about Security/Defense/Knox/Bootloader/TrustedApps and various other items
- Part 2 contains a dump of source code and related data about device security and encryption
- Part 3 contains various repositories from Samsung Github: mobile defense engineering, Samsung account backend, Samsung pass backend/frontend, and SES (Bixby, Smartthings, store)
A full list of what the hackers have:
- source code for every Trusted Applet (TA) installed in Samsung's TrustZone environment used for sensitive operations (e.g. hardware cryptography, binary encryption, access control)
- algorithms for all biometric unlock operations
- bootloader source code for all recent Samsung devices
- confidential source code from Qualcomm
- source code for Samsung's activation servers
- full source code for technology used for authorizing and authenticating Samsung accounts, including APIs and services


