Researchers have discovered a large number of comprised small office and home wireless routers. Hackers attacked more than 300,000 wireless router devices manufactured by D-Link, Micronet, Tenda, TP-Link and more. This discovery was made by researchers from a security firm 'Team Cymru' who has also disclosed a cross-site request forgery (CSRF) where attackers can access TP-Link routers using a blank password.
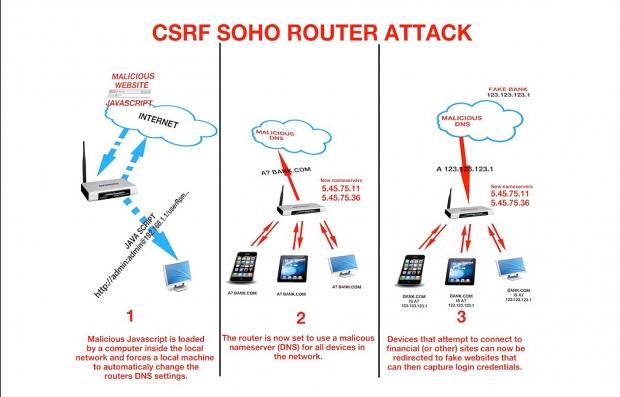
The idea is that hackers use multiple techniques to take over the wireless routers. Once the hackers get access, they change the domain name system (DNS) servers that's used to translate 'human-friendly' domain names into IP addresses for computers to track down web servers. The router re-directs to a fake website via the DNS where the unsuspecting victims insert login credentials. Once the credentials are inserted, the attackers use it to log into victims' accounts and uses socially engineering sms to induce the victim to unknowingly approve a transfer of funds to the attackers online banking account.
The hackers have attacked more than 300,000 routers located in multiple countries such as Vietnam, India, Colombia, etc. These compromised devices can now re-direct all of its end users to a malicious website to steal banking passwords. There is also a series of attacks that targets bank customers in Poland. It was found that fake DNS was used on the home and small office router which redirect computers, tablets and smartphones to a website made to collect online banking credentials from unsuspecting customers.
This requires effort from end users to secure their routers to prevent most of the attacks, at the very least for now. For users, the way to know if their home and small office is affected by checking if their DNS setting is changed to 5.45.75.11 and 5.43.76.36. DNS addresses 95.211.241.94 and 95.211.205.5 were also found to attack certain banks in Poland. Its also best if remote administration features are disabled on the routers if they're not needed. For those who use such features should limit the router's remote IP address to the one the end-user uses. This way only you can access it. Earlier, Tripwire said that almost 34% of top best-selling routers were being exploited because users do not change its devices' default username and password. Therefore, it goes without saying that people also change their default login credentials of their wireless routers. Its also best to update router's firmware, especially in the case like ASUS where they have released a firmware fix after months of a report being published of its vulnerability.
Its best if one keeps checking their DNS setting regularly to be sure that their routers are not compromised. It also being said that the router's web interface is disable as router interfaces are usually a suspect for cross-site request forgeries and other type of attacks. It should be noted that many such attack were highlighted in the past, irrespective of the brands. ZyXEL's ZynOS allowed attackers to download the router's configuration file from an unauthenticated GUI URL (https://[ipaddress]/rom-0) where the ROM-0 file is decompressed can be accessed easily. Once its done, the data of the router can be used through automated attack scripts that was easily available online to gain access to ZyXEL routers and change its DNS settings.