The developer of Notepad++ has furnished us with more information about how the popular text editor was compromised by hackers for some six months.
Ars Technica picked up the blog post which supplies further details about the exploitation of some Notepad++ users, which was leveraged via an "infrastructure-level compromise that allowed malicious actors to intercept and redirect update traffic destined for notepad-plus-plus.org".
Meaning that the compromise was enacted at the web hosting provider level, and wasn't a direct hack of the Notepad++ software itself - targeted users were redirected to download compromised updates, essentially.
This started in June 2025 and was the work of 'state-sponsored hackers' in Asia (likely China) we're told, with the shared hosting server remaining compromised until September 2. It seems the attackers kept a deliberately low-profile and flew under the radar in terms of using the exploit, which would be typical for a targeted campaign such as this, picking victims carefully.
Even after September, when the server access was cut off, the attackers still "maintained credentials to internal services" which was the case through to December 2, 2025, meaning they could continue redirecting update traffic for Notepad++ to their own malware-propagating servers.
As the blog post explains:
"The attackers specifically targeted Notepad++ domain with the goal of exploiting insufficient update verification controls that existed in older versions of Notepad++. All remediation and security hardening were completed by the provider by December 2, 2025, successfully blocking further attacker activity."
So, this is a problem that's now in the rearview mirror, but there's been a fair amount of misunderstanding about what happened here, mainly around this being a compromise of the Notepad++ client (which, as noted, it definitely wasn't).
Clearly, it's a worrying development, though, and a sophisticated attack, using an apparently novel payload that's been named 'Chrysalis' and was described by security outfit Rapid 7 as a "custom, feature-rich backdoor".
The author of the Notepad++ blog post explaining the investigation wrote: "I deeply apologize to all users affected by this hijacking."
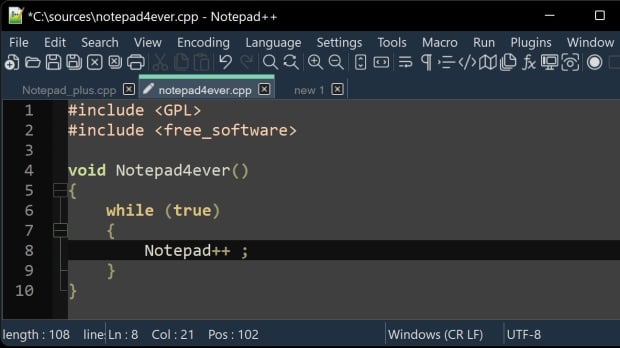
Notepad++ is a popular alternative to Windows Notepad, especially since Microsoft started turning the latter into WordPad (which is no more). And the question its many users will be asking is what they need to do now if they've downloaded, or updated, the client from June through to December last year?
The developer's advice is:
"I recommend downloading v8.9.1 (which includes the relevant security enhancement) and running the installer to update your Notepad++ manually."
The Notepad++ website has also been switched over to a new web hosting provider which has "significantly stronger security practices", the blog post informs us.