Here's why Apple thinks 8GB of RAM is enough in its latest Macs
If you buy a new M3 iMac or M3 MacBook Air at an Apple Store today, you'll spend more than a thousand dollars yet only get a machine with 8GB of RAM - unless you choose to upgrade to a more copious amount and pay extra, of course. That's something that Apple has long drawn flak for with many Windows PCs and laptops shipping with more, especially at the same kind of price point. However, Apple has now suggested that there is a very good reason these Macs come with just 8GB of RAM - that's all that people really need.
At least, that's what most people who buy these particular Macs need, according to two Apple executives who were interviewed by IT Home.
According to the IT Home report, Mac marketing executive Evan Buyze argued that the entry-level 8GB of RAM in iMacs and MacBook Airs is plenty for most tasks and most users. He used some examples as well, saying that media playback. photo and video editing. and even gaming only needs 8GB assuming you aren't pushing the boundaries - high-end games might need more, but it's unlikely anything downloaded from the App Store and Apple Arcade, will. Web browsing is another key use, and 8GB is plenty for that, too.
Continue reading: Here's why Apple thinks 8GB of RAM is enough in its latest Macs (full post)
MSI's new MPG EZ120 ARGB fans are magnetic and join together, requiring only a single cable
Thanks to innovative new designs, DIY PC building continues to improve, especially when putting together a gaming rig decked out with multiple fans, ARGB lighting, and modern components. MSI's new MPG EZ120 ARGB Fans fall into the recent cable-free school of system fans that let you daisy-chain and connect multiple fans without worrying about cable management.
This is awesome because a traditional ARGB fan requires connecting a system fan header to your motherboard or fan controller and a separate ARGB header. When you start adding multiple intake and exhaust fans, this can quickly become a cable management problem. MSI's new MPG EZ120 ARGB fans have a custom JAF 7-pin header that integrates ARGB and system fan headers.
It doesn't stop there. The MPG EZ120 ARGB fans are magnetic, so joining one, two, or three is a breeze - with unique Magnetic Connector Blocks delivering power and facilitating the signal between the fans.
Elgato's limited edition Fallout gear includes a custom Stream Deck and mic, and we want them
With the release of the Fallout TV series on Prime Video, a Fallout 4 remaster coming later this month, and everything post-apocalyptic still as popular as ever, Elgato has just launched a new limited-edition line-up of Fallout gear created in collaboration with Bethesda. The line-up includes a Fallout Edition Stream Deck, Wave DX, Wave XLR, and Wave Mic Arm LP.
This is the first time Elgato has developed a custom dynamic microphone, audio interface, or boom arm, so it's also offering Vault Overseer Kits that bundle the new Fallout gear. But it doesn't stop there, as Elgato and Bethesda are offering some very cool bonus digital goodies for fans that draw on the franchise's long history of mods and customization.
Available separately and free for all Elgato users (via the Elgato Marketplace), you can now download Pip-Boy-inspired icons for the Stream Deck, Vault-Tec Stream Deck screensavers, and a voice modifier that includes several presets and settings to make you sound like another wastelander wandering the wastes.
BIOSTAR becomes the latest Intel GPU partner, launches Arc A750 OC graphics card
BIOSTAR is the latest GPU maker to join the Arc family with the new BIOSTAR Arc A750 OC mainstream graphics card. BIOSTAR, which has several GeForce RTX and Radeon RX cards available, is now offering a new mainstream GPU with its Arc A750 offering.
As an OC model, it boosts the graphics clock speed to 2200MHz, a 7% increase over Intel's reference spec. Elsewhere, it's your typical Intel Arc A750 GPU with 8GB of GDDR6 memory on a 256-bit interface, 28 Intel Xe-Cores, and a power rating of 225W.
The dual-fan BIOSTAR Arc A750 OC is a compact GPU, measuring 222 mm in length, 101 mm in height, and 2.2 mm in slot thickness. The minimal rectangle and black design look pretty stylish, too, thanks to the all-blue PCB, reminiscent of Sparkle's Intel Arc line-up.
ASUS's latest ProArt Display is a 32-inch 8K Mini LED HDR beast for professionals
Professional displays are very different from those designed for gaming, where response times, refresh rates, and VRR support sit pretty high on the list. Professional displays are about accurate and vibrant color reproduction for designers and professionals to create and edit with reference-quality visuals.
At the NAB Show 2024, ASUS was on hand to present its latest professional monitor, the new ProArt Display PA32KCX - described as the "world's first 8K HDR Mini LED monitor with LuxPixel Technology." The 32-inch display features a native 8K resolution (7680 x 4320) with a 4096-zone Mini LED backlight, 97% of the cinema-grade DCI-P3 color gamut, 1200 nits peak brightness, and 1000 nits full-screen sustained brightness.
That last bit makes it one of the most impressive 32-inch displays for 2024 and perfect for HDR workflows. It's a tasty display and comes packed with ports. It has HDMI 2.1, DisplayPort 2.1, a USB hub, and dual Thunderbolt 4 USB Type-C ports with up to 96W Power Delivery.
More people are buying classic Command and Conquer RTS games than new releases
There has been a lot of negative talk lately about the current state of the videogame market. The most popular and played games are several years old, titles like Fortnite, Counter-Strike, Apex Legends, and other popular competitive and online games. Outside of a few exceptions, new games are struggling to find an audience, and as budgets increase dramatically, the risk for developers and publishers to launch something new is on the rise.
Looking at the best-selling games, new titles are few and far between. In Europe, half of the top 10 best-selling games for March 2024 were old Command & Conquer games. Throw in Grand Theft Auto 5, which continues to sell, and Ubisoft's aging Tom Clancy's Rainbow Six: Siege - old games are selling.
The best-selling title for the month was EA Sports FC 24 (the FIFA replacement), with Helldivers 2 in second place and Dragon's Dogma 2 in third place - the latter debuting in March. After that, five Command & Conquer games are on the list, which is impressive because the European data includes PCs, consoles, and digital data from storefronts like Steam, Xbox Live, PlayStation Network, and the Nintendo eShop.
Blackmagic's new URSA Cine 12K camera shoots 12K video at 90FPS for $15,000
Blackmagic showed off some new cameras at the 2024 NAB Show in Las Vegas, including the new Blackmagic URSA Cine 12 K, which was designed from the ground up as its new high-end digital camera. It costs $15,000.
The new Blackmagic URSA Cine 12K has a wide variety of inputs and outputs, including 10GbE ethernet and dual M.2 SSD slots for some super-fast, massive SSDs to handle the 4K, 6K, 8K, and 12K video you can capture with it. The company has a bunch of new design tweaks on the URSA Cine 12K, with all configurations on the camera done through locking nuts, making it easy to put it on a tripod, slider, or go handheld shooting 12K video.
Inside, Blackmagic built a completely new 12K 35mm large-format sensor for the URSA Cine 12K camera, supporting five different 12K formats. The 12K resolution itself is an eye-popping 12,288 x 6912 for the 16:9 aspect ratio, up from the 8192 x 4608 capable of 8K full frame with a 16:9 aspect ratio. Impressive stuff.
LG expands self-developed on-device AI chip, will go into 46 products in LG's product families
LG has announced plans to expand its home appliance-specific on-device AI chip -- DQ-C -- to 46 models through 8 product families.
The new LG DQ-C chip supports AI control, LCD display driving, and voice recognition and is specialized for operating systems inside of home appliances. LG has designed the DQ-C AI chip in-house, with previous chips produced by other semiconductor companies, while LG outsources to TSMC on its 28nm process node in Taiwan to make its DQ-C AI chip.
LG has spent three years deep inside research and development of the DQ-C chip, first announced in July 2023, and is used inside of five LG products including washing machines, dryers, and air conditioners. LG first introduced washing machines and dryers with its DQ-C chip under its Home Appliances 2.0 series in July 2023, showing off the actual DC-Q chip at IFA last year.
Overwatch 2 is finally punishing players who leave mid-match, more tweaks with Season 10
Blizzard is making some more changes to Overwatch 2, with its upcoming Season 10 to see changes to the game that will punish players who leave a game mid-match... finally.
Starting with Overwatch 2 Season 10, the developer is taking a "firm stance" on leavers in Competitive Play, with a new update for that game mode, too. Starting with Competitive Play, with Overwatch 2 players being suspended from Competitive Play whenever they leave a Competitive Play match, with a ban of 15 minutes.
But, if you leave more games, that penalty gets harsher and harsher: 2 games left out of 20 games, there's a 2-hour ban, while leaving 3 of your last 20 played games results in a huge 8-hour ban. From there, leaving 4 out of the last 20 games played will see you with a whopping 20-hour ban, while leaving 5 games out of the last 20 played results in a major Competitive Season BAN, while 10 games left throughout the entire season (at play) will result in a Competitive Season BAN.
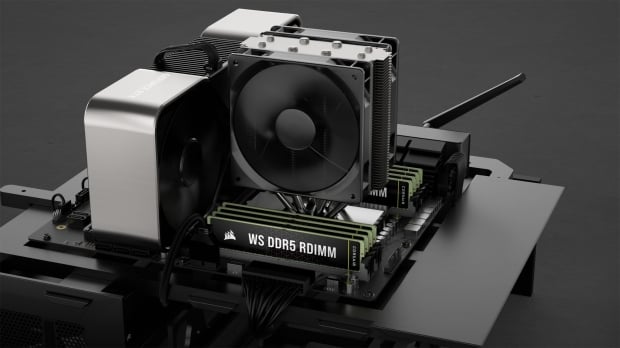
Corsair unveils its first DDR5 workstation RAM with new WS DDR5 RDIMM ECC memory kits
Corsair has just announced that it has entered the DDR5 workstation memory market, with the introduction of its new WS DDR5 RDIMM memory kits.
The new Corsair WS DDR5 RDIMM memory kits have been engineered to offer uncompromising performance and reliability. They are compatible with Intel's new 4th Gen Xeon and AMD Ryzen Threadripper 7000 series CPUs. If you want to fill every DIMM slot of your motherboard, they come in huge 256 GB DDR5 memory kits.
Corsair says that with its memory kits coming in huge 256GB capacities, it will set a new standard for memory-intensive tasks like high-resolution media editing, 3D rendering, and of course, AI training. Corsair has carefully screened each DIMM, with the modules passing JEDEC specifications with higher timings and higher speeds, making sure you get the optimal performance for the huge workloads these DIMMs will crush.