A security researcher going by the alias Nightmare-Eclipse has uncovered a zero-day exploit they describe as one of the most insane discoveries ever, saying it "almost feels like a backdoor." Dubbed YellowKey, the exploit allows anyone with physical access to a Windows 11 system to bypass default BitLocker protections and gain complete access to an encrypted device within seconds.
BitLocker is Microsoft's full-volume encryption that protects storage disks and their contents from anyone without the decryption key. That key is stored in a Trusted Platform Module (TPM), and BitLocker is a mandatory protection for many organizations, including government contractors.
The researcher refers to it as a backdoor because the bug appears only in WinRE (Windows Recovery Environment) and not in Windows itself, which lacks the required functionality needed to trigger the bypass. Additionally, the bypass affects only Windows 11, Windows Server 2022, and Windows Server 2025 systems with the default BitLocker configuration, while Windows 10 machines are unaffected.
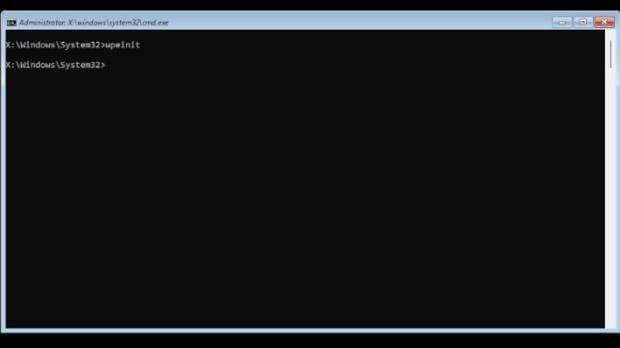
The core of the YellowKey exploit involves a custom-made FsTx folder that provides transactional atomicity for file operations. An attacker only needs to copy the FsTx folder to a specific path on a recovery drive, boot into WinRE, and follow a simple key sequence. This opens a command prompt with full access to the entire drive's contents, allowing an attacker to copy, modify, or delete files. Normally, at this stage, a BitLocker recovery key would be required, but YellowKey bypasses that safeguard entirely.
Multiple researchers have confirmed the exploit works as described, though researcher @KevTheHermit on X notes it can be inconsistent and may require repeated attempts. The same researcher also released a second exploit, GreenPlasma, which is said to enable privilege escalation to the SYSTEM level by abusing trusted paths used by services and kernel drivers. Full proof-of-concept code was not published due to the potential for severe abuse.
That said, YellowKey only works with Windows 11's default BitLocker configuration, in which decryption keys are stored solely in the TPM. Users who rely on additional authentication at boot, such as a PIN or USB security key, are generally better protected against this kind of attack.




