This year, so far, has not exactly been a stunning display for Macs. Between the Flashback malware and now this, it really shows just how weak the security of Mac OSX is. The latest blunder by Apple and its security team is that they turned on a debug log file which stores the user's password outside of the encrypted area.
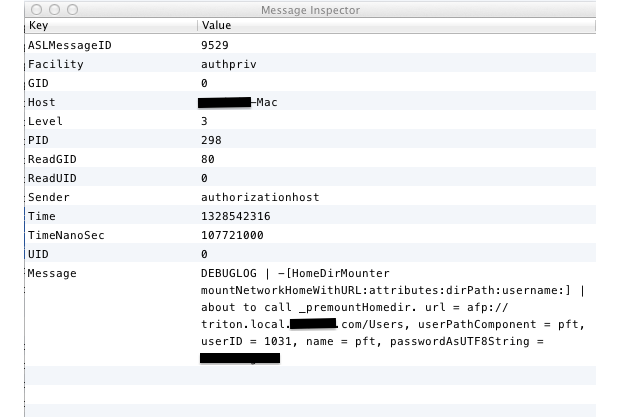
If you were using FileVault prior to upgrading to Lion, it may be time to think about changing your passwords as this would affect you. FileValut 2 users (whole drive encryption) are not affected by this accident. Additionally, if you have Time Machine backups, the plaintext log file has stored your password for the long term.
Security researcher David Emery explains:
This is worse than it seems, since the log in question can also be read by booting the machine into firewire disk mode and reading it by opening the drive as a disk or by booting the new-with-LION recovery partition and using the available superuser shell to mount the main file system partition and read the file. This would allow someone to break into encrypted partitions on machines they did not have any idea of any login passwords for.
Ironically, someone had posted on the Apple Support Communities after he noticed the flaw exactly 3 months ago. Not a single person had gotten back to him. This highlights Apple's quality assurance problems. This needs to be fixed fast. But even after a patch is released, it will be impossible to make sure all copies of the log file are deleted, so remember to change your password!


