A security researcher has claimed they have discovered significant vulnerabilities within Intel's websites, leading to the exposure of sensitive data on every single employee at the company.

The claims originate from security researcher Eaton Z, who outlined their findings in a blog post. According to the researcher, they discovered a business card portal that failed due to manipulation attempts, which resulted in Eaton being able to access deeper into Intel's database. Eaton writes that they were able to download a file of nearly a gigabyte in size, which contained the personal details of Intel's 270,000 employees.
Notably, Intel recently reduced its headcount size to 75,000, down from 109,800 at the end of 2024. So, if Eaton's reporting is correct, the file contains sensitive data on more than just Intel's employees. The sensitive data included roles at the company, addresses, phone numbers, and managerial positions. Furthermore, the vulnerability wasn't exclusive to one portal, as Eaton says three other Intel websites suffered from the same issue.
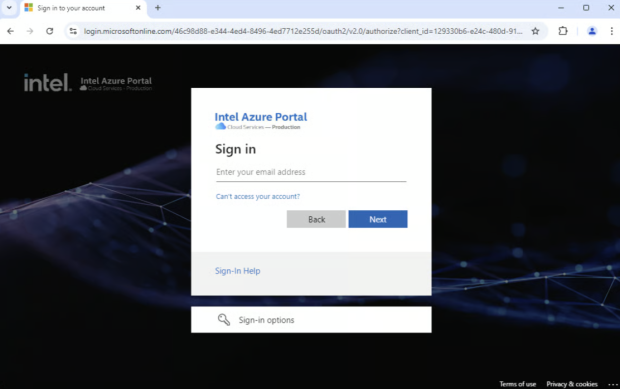
Eaton writes that internal sites such as "Product Hierarchy" and "Product Onboarding" portals were easily decrypted, along with another corporate login page for Intel's supplier site, revealing further critical details about Intel's internal workings.
Eaton contacted Intel about these gaping holes in its network in October 2024, and the company implemented fixes by late February 2025. Unfortunately, Eaton didn't receive any bug bounty compensation for pointing out the vulnerabilities within Intel's network, as Intel's bug bounty program excluded these cases under specific conditions. Eaton wrote that the only communication he had with the company regarding the discoveries was an automated response.




