Another day, another story where the world that people believe to be so innocent, isn't.
Israeli surveillance company NSO Group has experienced a gigantic, world-changing leak. The Guardian along with 16 other media organizations have run an investigation, showing that NSO's hacking software knock as "Pegasus", crafted to be used against terrorists and criminals -- just like all that "good" "hacking software" -- has been used against the good guys.
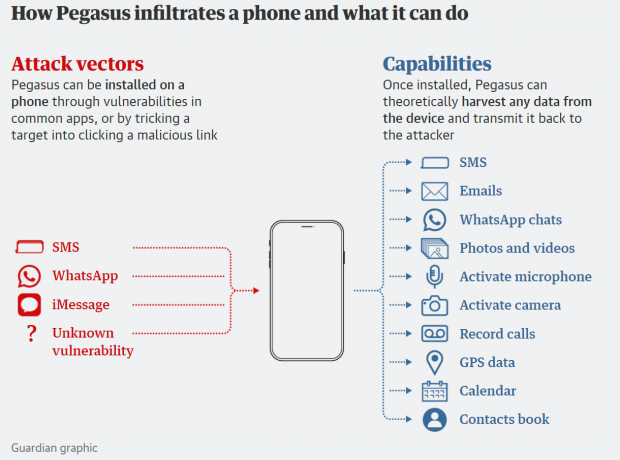
But first... what is Pegasus? Pegasus is malware that was made by NSO Group that can infect virtually any iPhone or Android smartphone and once installed, can let the operator pull out messages, photos, emails, record and monitor calls and even secretly activate microphones on the phone.
But now Pegasus has been used by the wrong people, with a leaked list of over 50,000 phone numbers of some of the most important people in the world. NSO's government clients were targets of the malware, in "surveillance attempts" according to a reporting consortium led by Paris-based nonprofit media organization Forbidden Stories, along with Amnesty International.
Who's at risk? Well, that is the scary part -- The Guardian and its media partners have said that in the coming days they'll reveal the identities of people who were on that list. But the list is large, and it includes "hundreds of business executives, religious figures, academics, NGO employees, union officials and government officials, including cabinet ministers, presidents and prime ministers".
There's even the personal phone number of a close family member of a particular country's ruler, which means that the ruler in question, has requested their intelligence agencies to spy on their own relatives.
Included in the data is over 180 journalists, with editors, reporters, and executives from the likes of Financial Times, CNN, the New York Times, France 24, the Economist, Associated Press and Reuters.
An analysis of the leaked data by the consortium reveals that at least 10 governments were involved, and they were NSO customers who entered phone numbers into the system. These countries include: Azerbaijan, Bahrain, Kazakhstan, Mexico, Morocco, Rwanda, Saudi Arabia, Hungary, India, and the United Arab Emirates (UAE).
It's not just phone numbers, emails, and photos -- Pegasus also gives access to your GPS and hardware sensors inside of your phone. This means that if you've had the malware installed onto your phone, one of NSO's clients will have a full log of your movements (past, present, and future) as well as real-time location tracking. Perfect for an assassination, well -- what we in the world will hear about as an "accident".
The Guardian reports that the "The latest advances in NSO's technology enable it to penetrate phones with "zero-click" attacks, meaning a user does not even need to click on a malicious link for their phone to be infected".
Right, because that's not scary.
Neither is this nugget: "Guarnieri [Claudio Guarnieri, who runs Amnesty International's Security Lab] has identified evidence NSO has been exploiting vulnerabilities associated with iMessage, which comes installed on all iPhones, and has been able to penetrate even the most up-to-date iPhone running the latest version of iOS. His team's forensic analysis discovered successful and attempted Pegasus infections of phones as recently as this month".


