We're all familiar with the passwords that should never, ever be used - like 'password' for example - but people still employ such cringeworthy efforts, and so do big organizations, it seems.
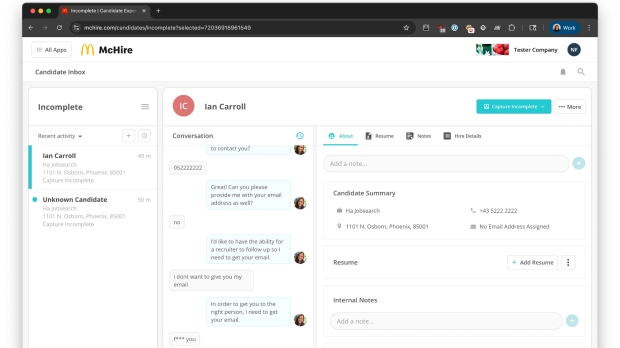
In this case, as TechSpot reports, a security researcher, Ian Carroll, managed to gain access to an admin account for the McHire platform, used to facilitate recruitment for McDonald's. It does this using a chatbot (Olivia) made by Paradox.ai.
Carroll achieved this when looking at the portal for McDonald's restaurant owners to log in to view their applicants, where there was also a link for Paradox.ai staff to log in. Clicking through to the latter, and using '123456' for both the user and password allowed a successful sign-in - to the researcher's disbelief - but only to a sample restaurant and related details (for internal testing).
While examining test conversations with the chatbot in this account, Carroll noticed an "interesting API to fetch the candidate information" and observes in a blog post:
"The main parameter of this request was the lead_id of the chat, which for our test applicant was about 64,185,742. We tried decrementing this number, and were immediately faced with PII from another McDonald's applicant (including "unmasked" contact data)!"
Using this method, the researcher could now access 64 million applicants and various personal details, all in unencrypted form. That included their name, email address, phone number, address, and the authorization token to log on as the user in the consumer portal, giving access to their chat messages to the bot.
Worrying? Yes, very much so for those who have applied for a role via this system.
The security hole was quickly shut down as soon as Carroll informed both McDonald's and Paradox.ai of the problem, as you'd expect. Still, this is one of the more eyebrow-raising security fumbles we've ever seen, without a doubt.