It seems no one is safe from the mighty DDoS anymore, and you don't even have to use anyone's bandwidth to accomplish that feat either. A flaw in WordPress's pingback feature has allowed a layer 7 (the application layer) DDoS take down, and effect, nearly 26,000 different sites using the CMS.
The attackers are flooding the sites with HTTPS requests, in this case pingbacks, that the server will log to the database and try to process. Being HTTPS means that more resources are being used to establish an SSL session, which devotes those resources to those tasks. Enough requests and the site can slow down to a crawl because the physical server just isn't fast enough. Not as much network bandwidth is needed to send these packets, so at the network layer it may look like normal traffic. But even 10,000 HTTPS requests per second can take offline even a modestly powerful server.
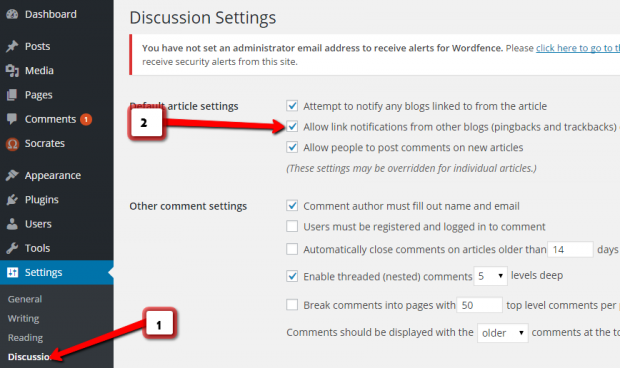
Thankfully the solution is relatively simple. Just turn-off pingbacks on your site altogether. At the very least change your .htaccess file to whitelist only the known and good IP addresses that are within your own community, those that aren't part of a botnet. Apparently the application layer DDoS attack accounts for around 13% of all DDoS attacks according to Sucuri. That's a lot more than you might think.