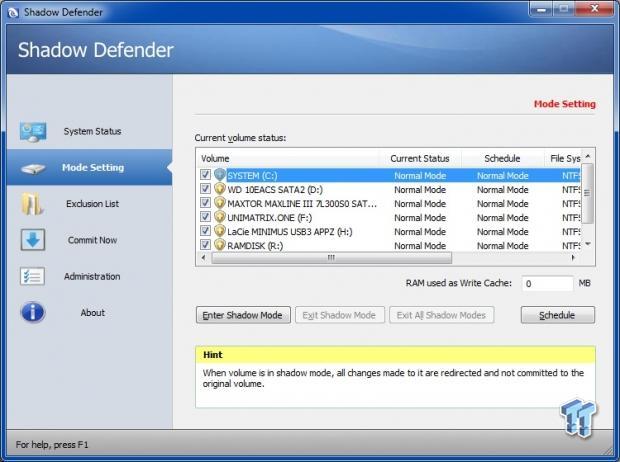
We have recently reviewed Shadow Defender, a light-virtualization program with a difference. SD (as it is known among fans) sandboxes whole disks/partitions and protects them against unwanted changes. All changes (including most malware infections and their effects) actually happen within the SD buffer, a virtual environment which resides in an area isolated from the real system. Upon reboot, the virtualization buffer is emptied by default and all volume changes are immediately discarded. The real volume remains untouched and Windows boots back to its normal clean state.
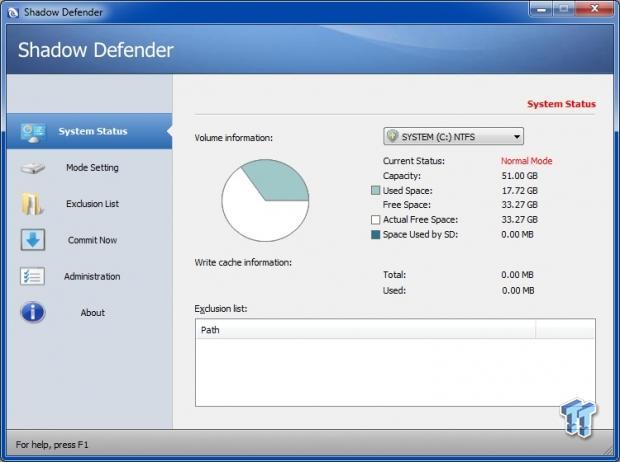
SD is essentially a final safety net for Windows systems. It also features a handy RAM cache, which means that you can now have a superfast virtual Windows environment running directly from RAM. When using such a RAM cache setup, your disks take no write hits, something that is very beneficial for devices like SSDs and flash sticks.
SD is a great piece of code, but threats keep evolving constantly. It is essential for SD to also keep evolving in order for it to continue to be relevant. Since October last year, I had the pleasure of exchanging ideas with Tony, the Shadow Defender developer. Some of my ideas have now already been implemented in current SD versions, e.g. the user-configurable RAM buffer for the virtual system, plus cache encryption.
The next step is to try and make SD a bit more future-proof. I brainstormed forums for ideas and the SD fans have offered their suggestions. The most crucial of those came from a user named "The Shadow" at Wilders Security Forum. He suggested options inspired from the way Sandboxie works; but whereas Sandboxie offers application-level sandboxing, with SD we are able to sandbox whole disks. Just like Sandboxie, SD should be made able to strip admin privileges from programs and to block kernel-level driver installs and application hooks. With such features, SD will provide a more proactive level of security, essentially prohibiting all malicious installations. The virtual system would always remain clean.
The next question in my head was this: What happens if a future smart malware finds a way to bypass those new options and infects the virtual system after all? In this case, the software should ensure that there can be no leaks to the real system. So, how to stop a malware from gaining a foothold in the real system? This can only be achieved with 100% full disk virtualization. If all sectors are being virtualized, there will be no space where the malware can store malicious code between reboots. In my mind, this is an essential security feature that can possibly be implemented into a future SD version and other similar software.
The SD developer is currently considering adding these features to a future version. Tony wants to keep SD simple and user-friendly, but there is an obvious balance there. SD has to keep updating itself with new features in order to remain current. The program is already the best against sophisticated threats. If Tony manages to crack those advanced features as well, then we'll be reaching a whole new level of proactive system protection.
Such options would give us a supercharged future Shadow Defender, one that offers comprehensive system security for both the real and the virtual system.

