Micron has been hit with a lawsuit that alleges the company engaged in a scheme to intentionally seek and destroy the reputation of a rival memory maker.
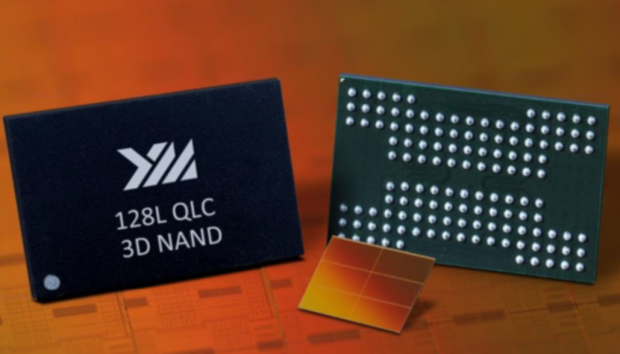
Chinese company, Yangtze Memory Technologies (YMTC) has filed a complaint in the US District Court that claims Micron participated in a scheme to destroy the company's reputation and business through "spreading xenophobic lies that YMTC's market-leading flash memory chips are capable of being used to spy on millions of Americans who use the devices in which the chips are embedded, at the behest of the Chinese Communist Party or its People's Liberation Army."
The lawsuit states YMTC's chips are completely safe and these accusations from Micron are "false and unlawful" - even going as far as to say Micron knows they aren't legitimate claims.
Public affairs firm DCI is also embroiled in the lawsuit, with YMTC alleging that DCI runs the website China Tech Threat, which featured some of the material YMTC highlighted in the lawsuit as slanderous. YMTC alleges China Tech Threat is secretly run by DCI and that Micron worked with the public affairs agency to post the illegitimate material.
YMTC pointed to one piece of allegedly slanderous information on China Tech Threat, titled "Silicon Sellout: How Apple's Partnership with Chinese Military Chip Maker YMTC Threatens National Security." The suit adds that there are plenty more articles similar to the one listed above present on the website.
"YMTC would have absolutely no ability to manufacture a chip in such a way as to clandestinely utilize those parts of a mobile device without the device manufacturer knowing," the complaint states
Moreover, the lawsuit states that since Micron and DCI possess significant technology knowledge of the products both companies are selling, they must know the claims they are making, specifically regarding YMTC's chips being used to spy on Americans, are incorrect, particularly since memory doesn't have the necessary components to exfiltrate data.
In layman's terms, traditional memory chips, such as NAND flash or DRAM, are passive components used to store data. Since they lack other elements such as CPUs, radios, or network interfaces, or the logic circuits to detect and package the data, they are unable to exfiltrate data.
For memory chips to be able to exfiltrate data, they would need to have hidden exfiltration circuitry, or a means of communication e.g, RF transmitter, USB signals, network access. However, device manufacturers such as Apple or Samsung vet this hardware rigorously, and would be able to detect any hidden exfiltration hardware as flags would be raised during the validation process.
With that being said, it isn't totally impossible. Compromised firmware could lead to a controller leaking data under the right conditions, especially if the state intelligence services are involved and working with the memory chip maker to create an unknown, and yet to be detected, form of hidden communication.





