GoDaddy is having more trouble with their DNS. After a major outage took down a large portion of the internet, they are again facing issues. This time, DNS records of websites hosted on GoDaddy are being modified. The modification adds subdomains that point to infected websites under the control of malicious users.
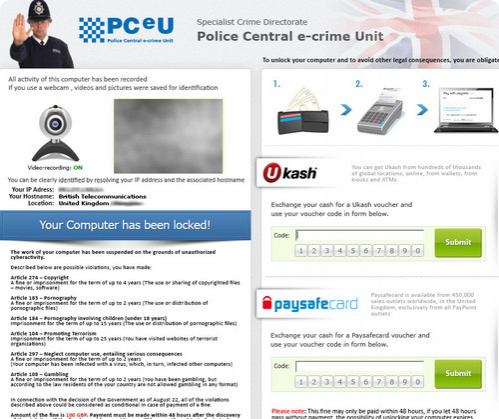
Once a computer is redirected to the malicious IP, the server attempts to exploit the system using the Cool Exploit kit. Because of the record being modified at the DNS level, the URL and site look to be legitimate. If a user becomes infected, the computer is locked down via ransomware and the user is made to pay to unlock it.
It's the typical ransomware setup--it uses local currency and information to make it look as if local law enforcement are the ones who locked it down. Affected webmasters should check their DNS records to make sure that they don't have these rogue subdomains and users who have been affected should contact a virus removal expert.
Update:GoDaddy has provided me with the official statement regarding the breach:
Go Daddy has detected a very small number of accounts have malicious DNS entries placed on their domain names. We have been identifying affected customers and reversing the malicious entries as we find them. Also, we're expiring the passwords of affected customers so the threat actors cannot continue to use the accounts to spread malware.
We suspect that the affected customers have been phished or their home machines have been affected by Cool Exploit as we have confirmed that this is not a vulnerability in the My Account or DNS management systems.
Go Daddy highly recommends that US- and Canada-based customers enable 2-Step Authentication to help protect their accounts. Details on how to set up this feature are located at https://support.godaddy.com/help/article/7502/enabling-twostep-authentication.
If a customer suspects their account may have an issue, we encourage them to contact Go Daddy Customer Care or fill out the form at the following link: https://support.godaddy.com/support/?section=support.


