Hacking, Security & Privacy News - Page 23
PlayStation 4 jailbreak is here, confirms hacker on Twitter
A Twitter account with no profile photo and just over 2,000 followers called 'Cturt' has confirmed a Sony PlayStation 4 jailbreak success recently, telling the public that the "PS4 kernel exploit [is] finally working! Thanks to everyone involved!"
This jailbreak is said to enable a few interesting and helpful features, with CTurt explaining that this new breakthrough will enable users to "successfully dump RAM from other processes (like SceShellUI) using ptrace," further explaining that he will next be working on patching RAM.
While there is no posted guide, links or information as to how users can complete the same process on their consoles, there is a GitHub page of the same name, linked in the Twitter, where this information may surface in the near future. This news is exciting for developers looking at making custom firmware for the PlayStation 4, further opening up many other coding possibilities for community advancement of this device.
Continue reading: PlayStation 4 jailbreak is here, confirms hacker on Twitter (full post)
US Government department still hasn't notified all of its hack victims
A recent hack and theft of Government files sent a US Government department into a frenzy in recent past, with further developments urging a spokesperson to inform the public that not every victim has or will be notified of this data breach just yet.
While the Government is meant to be notifying each victim of this breach from May 2014, around 7 percent of the 1.5 million people in danger are currently unable to be contacted. This is said to be due to them moving house or being without a Government-recorded address. Confirmed by the Office of Personnel Management, being the place that was hacked, this notification system is obviously not flawless.
The original hack was traced back to China but wasn't discovered or announced until one year after its occurrence, with the names, addresses, social security numbers and various other pieces of information about employees, contractors and job applicants being now in the hands of an unverified source.
Continue reading: US Government department still hasn't notified all of its hack victims (full post)
Hollywood slightly alters its anti-piracy rules
Appointed as a representative for six major Hollywood studios, The Motion Picture Association of America (The MPAA) has published new anti-piracy guidelines, addressing how they are slightly loosening the noose on cinemas and more.
Set to target those who film movies while at the cinema, The MPAA is now telling these facilities that calling the cops on recorders is now an optional endeavor, previously ordering workers to call law enforcement immediately. While this policy is targeted mostly at handy cam users looking to leak movies on torrent websites, The MPAA has included recording devices of any kind, including Google Glass.
The MPAA previously implemented a $500 'bounty' to workers who caught and apprehended pirates looking to steal content, with this also being removed in the latest update. While a bounty was a good token in the first place, the removal of a 'bonus' will possibly breed a negative culture within the cinema employees.
Continue reading: Hollywood slightly alters its anti-piracy rules (full post)
Russian hackers have scraped over $790 million in three years
Kaspersky Lab has reported that a group of approximately 20 Russian hackers has stolen $790 million recently. Around 70 percent of this money has come from individuals and businesses within USA and Europe since 2012, supplementing this income with the further 30 percent coming from Russian bank accounts.
Describing them as a highly organized and sophisticated syndicate, Intel Security's Mike Sentonas told News.com.au that "We've been tracking a lot of these groups for years now and they have such strong architecture it's hard to shut it down."
While hackers can be placed around the globe, Deakin University's Professor Mathew Warren claims that a major concentration of these criminals are located within Russia and the surrounding countries of Ukraine and Bulgaria.
Continue reading: Russian hackers have scraped over $790 million in three years (full post)
Windows Defender works against Dell adware certificate
While Dell recently admitted that a dangerous vulnerability was pre-installed on their systems, they refused to believe that it was created by them but still pledged to remove it.
In a great move my Microsoft, its Windows Defender security system has now begun locating and removing the certificate itself, as long as you've updated your Windows OS. Discovered by ZDNet in a routine action just this morning, Windows Defender identified a threat named "Win32/CompromisedCert.D" and removed it from the system.
Dell has reportedly started issuing updates to its maintenance utility to also rid this issue for all concerned, but it doesn't hurt to update Windows Defender to be safe.
Continue reading: Windows Defender works against Dell adware certificate (full post)
Security experts say Australia is a very easy hacker target
"Malicious hackers already know us to be weaker than the rest of the world," the director of Hacklabs, Chris Gatford, told News.com.au in an interview. He believes that without much effort, Australia's water and electricity supply lines could become a complete shambles with a single hacker attack.
Gatford went on to draw the comparison between Australia's national infrastructure and your mothers Microsoft Surface, stating: "It would only take a skilled individual to breach these computer systems, because more often than not they are not patched as frequently as corporate or home systems which have automated updates." While he did comment mainly on security concerns within Australia, Gatford also made mention of other technical mishaps around the world, touching on "historical examples of traffic lights being overtaken, denial-of-service attacks at airports and organisations in Wall Street coming under attack to see its 100 per cent possible."
The whole situation isn't quite as dire as it may initially seem though, the Hacklabs director did reassure us that these necessary utilities would recover quickly from attack, rather than send Australia into a Fallout 4-like existence.
Continue reading: Security experts say Australia is a very easy hacker target (full post)
Dell admits fault, promises to remove preinstalled security flaw
Described as an "unintended security vulnerability," Dell has admitted that a root certificate preinstalled on some of its models exists and promises to remove it.
A Dell spokesperson explained that "to address this, we are providing our customers with instructions to permanently remove the certificate from their systems via direct email, on our support site, and technical support," further commenting that the computer giant does not install malware on user systems pre-delivery.
While Dell claims no responsibility for this flaw, a security blogger by the name of Hanno Bock disagrees. He says that this root certificate is not only shipped within these pre-built machines, but it's under the name 'eDellRoot' and is linked to 'Dell Foundation Services' drivers.
Continue reading: Dell admits fault, promises to remove preinstalled security flaw (full post)
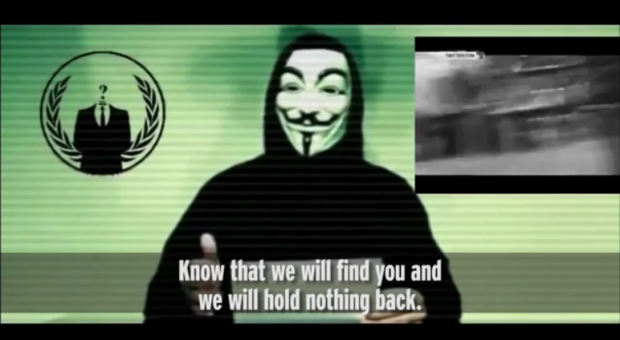
Anonymous vows revenge against ISIS for Paris terror attacks
Hacktivist collective Anonymous has reportedly declared war against the terrorist group ISIS, vowing revenge against the Islamic State following the recent terror attacks in Paris.
On the Saturday following the brutal attacks that saw more than 129 people murdered, ISIS took responsibility for the wave of terror that swept over the city of Paris. President François Hollande then confirmed the Islamic State's involvement. The terrorist group boasted that this wast just "the first of the storm" and called Paris a "capital of prostitution and obscenity."
Anonymous has now stood up to promise retribution, and has already begun wreaking havoc across the Islamic State's online network as part of the #OpParis campaign. "These attacks cannot be left unpunished. That's why Anonymous worldwide will track you," a recent Anonymous video proclaimed. "Yes, we are going to track you down, like we have since the Charlie Hebdo attacks. Wait, then, for a massive response from Anonymous. Know that we will find you, and we will hold nothing back."
Continue reading: Anonymous vows revenge against ISIS for Paris terror attacks (full post)
Hacker team remotely jailbreaks iPhone, wins $1 million
An anonymous hacker group has remotely jailbroken a new iPhone running iOS 9.1, winning themselves a cool $1 million from startup Zerodium (self-described as a "premium exploit acquisition platform"). The winnings are pending final verification of the exploit, but results at this stage look good.
To put the difficulty of this feat in context: a chain of zero-day bugs needed to be found, the hack needed to be remote (much more difficult -- Chinese hacking team Pangu already hacked the new iPhone, but couldn't do it remotely) and made through Safari, Chrome, or a text or multimedia message, and full system access needed to be obtained. An iPhone has not been remotely jailbroken for over a year, since iOS 7. Zerodium says Apple will likely patch these bugs "in a few weeks to a few months".
The winning team was one of two to take on the challenge. Both found themselves stuck, but eventually one found a way via Chrome and iOS, just a few hours before the challenge was to end.
Continue reading: Hacker team remotely jailbreaks iPhone, wins $1 million (full post)
256 iOS apps outed for privacy violations, to be removed from store
Researchers have discovered there are 256 apps on the App Store that have found their way around Apple's vetting process and violated privacy rights. All of them use the Chinese-developed Youmi SDK. In total, approximately one million people use the apps in question.
To be clear, the developer of any of these apps is not necessarily to blame at all. It appears Youmi is the one interested in acquiring your data, and has insidiously worked gathering tools into its development kit, thereby attempting to cover its tracks and pass the blame onto developers, should the scheme be uncovered.
Nate Lawson, founder of security analytics startup SourceDNA (which uncovered the violations), says this is "definitely the kind of stuff that Apple should have caught."
Continue reading: 256 iOS apps outed for privacy violations, to be removed from store (full post)