Hacking, Security & Privacy - Page 4
Stay informed with the latest hacking, cybersecurity, and privacy news, including data breaches, leaks, cyber attacks, and tips to stay safe online. - Page 4
Stay Updated
Follow TweakTown for breaking tech news, reviews, and daily updates.
As an Amazon Associate, we earn from qualifying purchases. TweakTown may also earn commissions from other affiliate partners at no extra cost to you.
4.3 million Americans are at risk of fraud after savings account data breach
The Office of the Maine Attorney General has been informed of a data breach that has exposed sensitive data of 4.3 million customers.
According to HealthEquity, the data breach exposed the below sensitive data that of millions of Americans, with the fintech firm saying that not all of the categories listed contained data for every person. Reports indicate the breach occurred on March 9, 2024, and that it was detected on March 25. After the breach was discovered HealthEquity conducted an internal investigation on the origin of the hack, tracing it back to an online data storage location that became compromised.
The compromised location led to the unauthorized party gaining access to a "limited amount of data stored in a storage location outside our core systems." HealthEquity doesn't believe the stolen customer information has been used nefariously, and as compensation to affected customers, HealthEquity is offering a two-year complimentary credit identity, monitoring, insurance, and restoration services.
Qualcomm's Adreno GPU vulnerability found: Snapdragon chips join problematic Intel, AMD CPUs
It started with Intel... then AMD... and now Qualcomm has been hit with multiple vulnerabilities inside of its Adreno GPU.
Google researchers have found vulnerabilities inside Qualcomm's Adreno GPU, which is the integrated GPU inside of its Snapdragon processors. The GPU has kernel privileges, which means the security flaws found could be significant, as it would allow hackers full control over your Qualcomm-powered device.
The researchers focused on GPU drivers because untrusted apps can access them without additional permissions, making them an easy target for hackers. The drivers complexity with the operating system makes things worse for users, but great (and easier) for hackers.
Russia-affiliated criminals use Sitting Duck technique to bag 30,000 domains
Since 2019, Russian-affiliated hackers have hijacked an estimated 30,000 domains since 2019, with the cybercriminals exploiting a flaw in DNS.
The vulnerability was detailed by security researcher Matt Bryant in 2016, who looked at how the vulnerability led to the hijacking of 120,000 domains. The same problem reared its head again in 2019 with GoDaddy, an internet domain registry, domain registrar, and web hosting company. The 2019 issue led to sextortion attempts and bomb threats.
The technique being used is called Sitting Ducks. It essentially exploits gaps in administrative privileges, enabling cybercriminals to alter domain records without any validation from the owner. Unfortunately, the hijacked domain isn't just damaging for the owner of the domain but also for any visitor to that domain, as hijacked domains are commonly used for phishing, scams, spam, and other illegal activity.
Microsoft confirms an attack brought down Microsoft 365 and Azure services
Microsoft confirmed via an update on its Azure Status website that a 9-hour outage was a result of a DDoS attack that affected its Microsoft 365 and Azure services.
The distributed denial-of-service (DDoS) attack affected the services globally, and within the blog post, Microsoft didn't specify where or who the attack came from. More specifically, the post states that while the initial DDoS attack did trigger the event, it was responded to by Microsoft's protection mechanisms, but following investigations, Redmond discovered "the implementation of our defenses amplified the impact of the attack rather than mitigating it."
Furthermore, Microsoft said that customer impact began at 11:45 UTC, and by 14:10 UTC, the fix was already rolled out, and the majority of the impact was successfully mitigated. The only details we have on how the outage occurred was Microsoft's description of the outage being caused by an "unexpected usage spike" that "resulted in Azure Front Door (AFD) and Azure Content Delivery Network (CDN) components performing below acceptable thresholds, leading to intermittent errors, timeout, and latency spikes."
Hackers steal and leak documents from Pentagon, Homeland Security, NASA, other US gov agencies
Hackers have leaked internal documents stolen from one of the largest IT services providers to the US government, Leidos Holdings.
Leidos Holdings recently learned of the hack, believing that the documents stolen were in a previously disclosed breach of a Diligent Corp. system it used, according to Bloomberg's sources, who asked not to be identified because the information isn't public. Leidos is reportedly investigating the issue now, the person added.
Now, the customers of Leidos are important: it includes the US Defense Department (DOD), the Department of Homeland Security (DHS), NASA, and other US and foreign agencies and commercial businesses. Leidos used the Diligent system to host information gathered from internal investigations, according to a June 2023 filing in Massachusetts.
Enterprise software provider exposed nearly a billion records in data breach
A non-password-protected database containing 769 million records was discovered to be exposed to the public, revealing critical information such as secret keys, bank account numbers, tax identification numbers, and email addresses.
Cybersecurity researcher Jeremiah Fowler discovered and reported on the database through a post on Website Planet, where he explained the database was owned by ClickBalance, one of Mexico's largest enterprise resource planning (ERP) technology providers. The database contained access tokens, API keys, secret keys, bank account numbers, tax identification numbers, and 381,224 email addresses. After informing ClickBalance about the database exposure, it promptly implemented restrictions.
Notably, ClickBalance is a software company that offers ERPs as a suite of cloud-based applications to enterprise organizations that enable those organizations to access those applications whenever they like across any device. These ERPs are typically used to manage different processes of an enterprise, such as finance, human resources, supply chains, manufacturing, sales, and other business operations.
Airline avoids CrowdStrike chaos because its systems run on Windows 3.1 and Windows 95
One industry that experienced the brunt of the recent CrowdStrike global IT outage, which put millions of Windows systems into a Blue Screen of Death loop, was air travel. In the U.S., nearly every flight was grounded once systems began to fail; however, one major airline was unaffected.
According to reports, Southwest Airlines systems were untouched by the CrowdStrike error because its various systems run on outdated versions of Windows.
Outdated is putting it mildly. Most of Southwest Airlines' systems run on Windows 3.1 - a version of Microsoft's operating system from 1992. Not only that, but the airline's most advanced system, its staff scheduling system, runs on Windows 95 - so it, too, was unaffected.
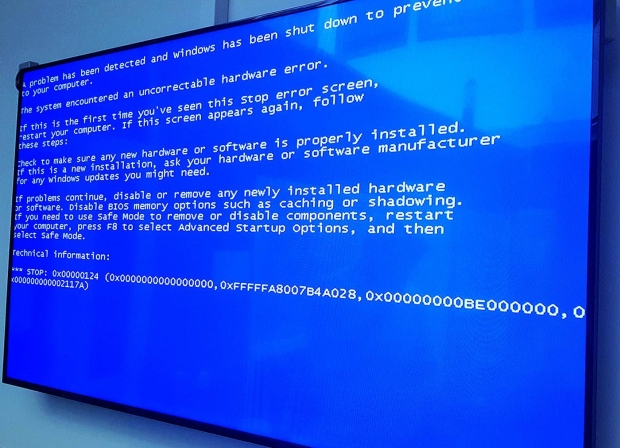
What caused the CrowdStrike Windows BSOD issue, and why it led to total system crashes
The world is still recovering from one of history's most disruptive IT outages. Millions of critical Windows-based systems across the globe are experiencing the dreaded Blue Screen of Death (BSOD). The system crashes affect banks, airlines, emergency services, supermarkets, and businesses, putting computers into an endless boot loop with no immediate recovery means.
The issue was quickly traced to CrowdStrike, which creates security software. An update to its popular security platform, Falcon, broke, leading to one of history's most extensive IT failures. The 'Falcon Sensor' component critically failed, resulting in no access to Windows. Critical systems used for point of sale, emergency services like 911, and airlines managing flights were rendered useless.
With the affected systems being Windows PCs, many have pointed fingers at Microsoft. However, the issue looks specific to CrowdStrike software and its update to 'Falcon Sensor.' So then, how did this crash Windows when other apps that fail Crash to Desktop (CTD)? And how can you fix the CrowdStrike BSOD issue? Let's dig in.
Breaking - Global IT outage grounds planes, closes banks, and disrupts services everywhere
A global outage is currently causing havoc, grounding planes, grinding public transportation systems to a halt, disrupting banking services, and affecting everything from streaming services to supermarkets. The cause is the dreaded Windows 'Blue Screen of Death' or BSOD, bringing down systems that countless people, businesses, and critical services rely on.
Based on reports, the culprit appears to be a CrowdStrike update for its CrowdStrike Falcon threat checker, which is currently causing systems to crash and fail.
This is one of the most significant outages we've seen in a while, it's gotten to the point where airlines like American Airlines, United, and Delta have stopped flights taking off. Emergency services are also apparently down in some areas.
Kaspersky hits back at US government over the banning of its products
In June the US government deemed the popular anti-virus software Kaspersky, which is used by millions of users around the world, a prohibited software as it was found to be a risk to national security.
In March 2022, the Federal Communications Commission (FCC) ruled that Kaspersky posed an "unacceptable risk to national security" due to its ties to the Russian government, which Kaspersky irrefutably denied. The anti-virus company denied having ties to any government and acts as an independent multinational company. Additionally, Kaspersky said the decision to ban its products across the United States was a purely political move.
The banning of Kaspersky by the Department of Homeland Security alleged the company has ties to the Russian government, presumably some kind of backdoor within its software that allows the Russian government access to devices running the Kaspersky software. Kaspersky responded by offering to reveal its source code to third parties for verification.
Continue reading: Kaspersky hits back at US government over the banning of its products (full post)
Microsoft officially approved this extremely dangerous door-opening malware
A product that was originally marketed as a security product has been discovered to be malicious malware that injects a kernel-level infection that makes the device susceptible to further attacks.
A new investigative report into the malware called HotPages revealed researchers notified Microsoft of the malicious software on March 18, and it has since been removed from the Windows Server Catalog of where it was once approved on May 1. However, up until that point, HotPage was presumably delivered to its victims as a security product, masquerading as an ad blocker called DWAdsafe for internet cafes in China.
HotPage contained malicious code that dropped a vulnerable system-level driver that could enable any attacker with the highest level privilege to execute new malicious code within a device. Additionally, the malware didn't even remove ads; it instead intercepted web traffic and redirected and manipulated content within a victim's browser. The malware hooked Windows API functions to intercept and modify browser activity to collect information on the victim, which was then sent back to the HotPage creator's server.
FBI confirms its gained access to the phone of Trump's shooter
The phone owned by Thomas Crooks, the man who shot and wounded former US president Donald Trump on July 13, has had his phone seized by the FBI, and now the US authorities have said they have gained access to the device.
July 13 marked the failed assassination attempt of former US president Donald Trump, who dropped to the floor after a bullet wounded his ear. Authorities identified the shooter as Thomas Crooks, a 20-year-old registered Republican, and the FBI later announced it acquired his phone.
The now-deceased Crooks didn't leave behind any obvious motive for his actions against the former president, which is why the FBI is hoping its newfound access to his phone may reveal his reasoning behind his actions, if Crooks was working alone or as part of a bigger group, and if there are any other attempts such as the one at the Pennsylvania rally planned for the future.
Continue reading: FBI confirms its gained access to the phone of Trump's shooter (full post)
Alarms raised in security circles after largest password leak in hacking forum history
Passwords may be one of the most annoying aspects of our daily lives, but they have become extremely important with the ever-growing adoption of the digital landscape. That is why it isn't good when nearly 10 billion unique plaintext passwords leak onto a hacking forum.
A user with the handle "ObamaCare," who has a history of leaking data such as employee databases sourced from law firms, and data acquired from colleges and casinos, posted on a hacking forum, "Xmas came early this year". The leaker added, "I present to you a new rockyou2024 password list with over 9.9 billion passwords!" ObamaCare is referencing a leak called "RockYou2021" where 8.4 billion passwords were leaked online.
Security experts over at Cybernews believe the leak could have extremely bad ramifications for users around the world, as the exposed users could see an increase in the number of online accounts being illegally accessed through brute force hacking. If you are interested in protecting yourself against such breaches, you can check if your password has been compromised using the Leaked Password Checker tool here.
Microsoft's new technology will use your eyes to decrypt secure documents
Microsoft has filed an interesting patent for display technology that effectively decrypts documents in real-time based on a user's gaze. Yeah, so at a glance, the encrypted document would be unreadable to anyone apart from the document's owner. The technology would decrypt the document in real-time based on where the user is looking - and only the components or sections they're currently looking at.
It takes the idea of the 'privacy screen' to a new level, as it isn't limited to hiding what's on screen for those sitting at an angle or behind someone in a public area but works in conjunction with document encryption and decryption.
As Windows Report spotted, the patent and documentation don't explain exactly how it will work. However, it will use a webcam and eye-tracking technologies to determine where you're looking and ensure that reading an entire document with this system isn't slow and laborious.
The biggest password leak in history just happened: 10 BILLION passwords leaked by hacker
On July 4 of all days, Independence Day for Americans, the largest password leak in history occurred, dubbed "RockYou2024" by the original poster "ObamaCare" on a leading hacking forum.
There are an incredible 9,948,575,739 passwords compiled all in plain text, close to 10 billion passwords, posted by user "ObamaCare". The user registered on the hacking forum in late May 2024, previously sharing the employee database from law firm Simmons & Simmons, a lead from an online casino AskGamblers, and student applications from Rowan College at Burlington County.
The team cross-referenced the passwords in the huge "RockYou2024" leak with the data from Cybernews' Leaked Password Checker, which the site "revealed that these passwords come from a mix of old and new data breaches". Researchers said: "In its essence, the RockYou2024 leak is a compilation of real-world passwords used by individuals all over the world. Revealing that many passwords for threat actors substantially heightens the risk of credential stuffing attacks".
The biggest ransomware attacks in recent history and the groups behind them
Ransomware is a popular form of malware in which files on a device, server, or computer system are encrypted, and the actors (often a hacker group or syndicate) demand a ransom to decrypt the data - and it's on the rise. According to ExpressVPN, ransomware payments exceeded 1 billion USD in 2023, the highest amount ever. In the age of generative AI, increasingly sophisticated encryption methods will see this figure grow even higher.
And then there's the rise of Ransomware-as-a-Service (RaaS), which is almost like a marketplace for ransomware tools and services - powered by the anonymity of cryptocurrency, the payment of choice for ransomware groups and hackers. The democratization of cyberattacks has opened the door to virtually anyone launching a cyberattack on unsuspecting individuals, businesses, or government bodies.
In recent years, large-scale ransomware attacks have targeted the healthcare industry, network security companies, Windows users, oil pipelines, and even Costa Rica. Here's a breakdown of the most notable.
Man busted stealing passenger data from in-flight Wi-Fi with 'evil twin' strategy
A man has been charged with stealing the credentials of people's social media and email services while on a commercial airline.
The Australian Federal Police (AFP) charged a man who was carrying a "portable wireless access device, a laptop, and a mobile phone" in his luggage. The AFP claims the man was attempting to scrape sign-in information from passengers aboard a flight by running a fake Wi-Fi network on a plane. The alleged man was reportedly creating fake Wi-Fi hotspots with SSIDs that were very similar to the network names found on flights, or an "evil twin".
When a user joined the network, they were prompted to input their credentials, which included email addresses and passwords that were then saved to the man's device. At the moment, authorities charged the man with unauthorized access to devices, along with "possession or control of data with the intent to commit a serious offense," which alludes to the man having the intention of using the data nefariously.
Microsoft hack was worse than it seems as more customers are told their emails were stolen
Microsoft confirmed it was breached on January 12, 2024, by hackers that gained access to Microsoft's corporate email accounts, leading to the theft of federal government email accounts.
While the hack was considered extremely bad at the time, and it still is, it appears the breach may be worse than initially anticipated as more Microsoft customers are receiving emails their email account has become compromised, meaning it wasn't just federal email account data stolen, but also customer data.
Microsoft blamed the attack on a Russian government-sponsored hacking organization called Midnight Blizzard, and according to the software giant, they are providing notifications to customers who were exposed to the hack through email correspondence with compromised Microsoft corporate email accounts.
Microsoft faulted for massive hospital record data heist by former employee
An American healthcare provider that serves more than 1.2 million people is concerned a former employee from the Microsoft-owned Nuance Communications stole sensitive data on more than a million patients.
Geisinger, an American healthcare provider for more than a 1.2 million people across Pennsylvania announced a security breach took place last year that was traced back to a former employee of Nuance Communications, the Microsoft-owned IT provider. Geisinger discovered the security breach on November 29 and immediately contacted Nuance Communications, which discovered the individual removed his access before the authorities were notified.
Nuance Communications then launched its own investigation and discovered the former was terminated from their position and then two days later accessed the sensitive records, making copies of records on more than a million Geisinger patients. The data includes birth dates, addresses, hospital admissions, discharge records, medical data, and demographic information. Notably, financial and insurance information wasn't stolen, according to Geisinger.
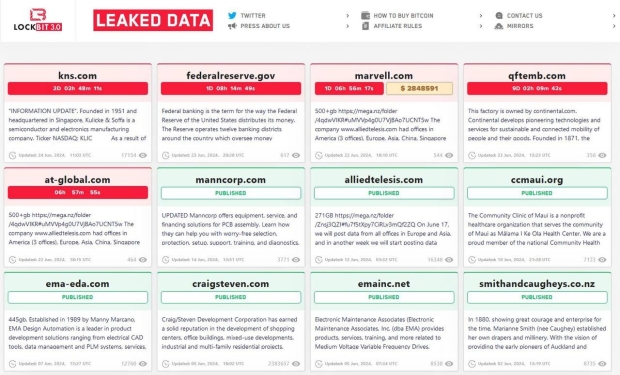
The United States Federal Reserve hacked: 33TB of data stolen by ransomware group LockBit
Uhh... so the United States Federal Reserve has been hacked, with a new post on a Dark Web leak site associated with ransomware group LockBit, holding 33TB of incredibly confidential financial data from the Fed.
On June 23, 2024 at 8:27 UTC, LockBit announced it had hacked into the systems of the Federal Reserve, with 33TB of sensitive banking information taken. The data includes confidential details of American banking activities, which if veritified, would make this one of the largest breaches of financial data in history.
The post reads: "Federal banking is the term of a way the Federal Reserve of the United States distributes its money. The Reserve operates twelve banking districts around the country which oversee money distribution within their respective districts. The twelve cities which are home to the Reserve Banks are Boston, New York City, Philadelphia, Richmond, Atlanta, Dallas, Saint Louis, Cleveland, Chicago, Minneapolis, Kansas City, and San Francisco".