Kaspersky of all companies have found something utterly shocking, an advanced cyber espionage network that makes last year's infamous Flame malware look like a joke. Dubbed Operation Red October, each attack is handcrafted for its victim in order to make sure it 100% works.
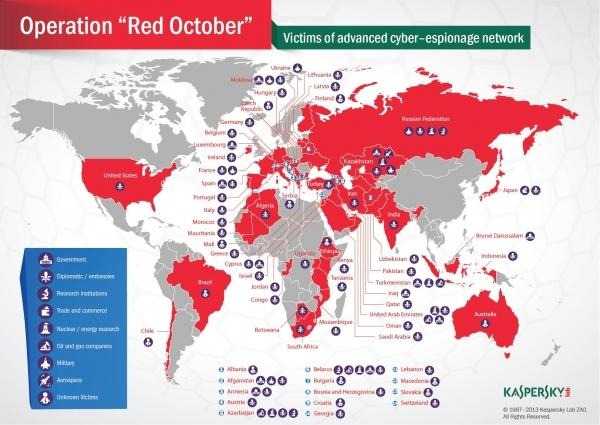
Red October has been hitting systems across the world since at least May 2007 and carefully chooses its victims spanning over two dozen countries who hold positions in government, military, aerospace, research, trade and commerce, nuclear, oil and other important, vital industries. Investigators aren't sure who is behind the attacks, but it is being reported that Chinese hackers may have created the exploit, while the various malware modules deployed seem to have been created by those who speak Russian.
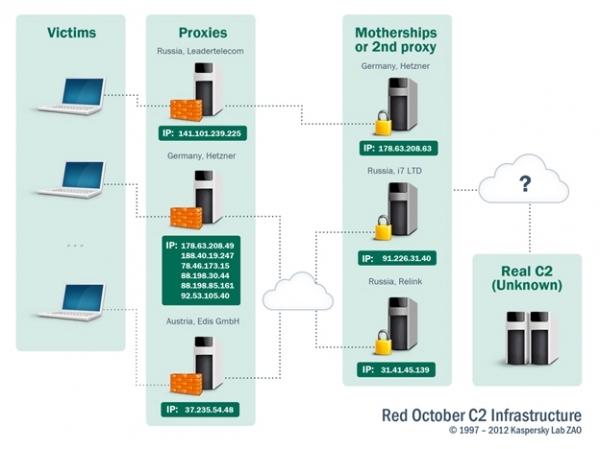
Kaspersky can't put their finger on the source, as it is currently being run through at least two layers of proxy servers across Russia, Germany and Austria. Whoever is involved has some skill, as they've been silently sitting, unknown to the user, in major government and industry computers.
While this exploit has been going, the hackers involved have been using two different exploits through Microsoft Word and Excel to infect targets through spear phishing schemes. After the system had been infected, the attackers would take whatever data they could through a bunch of persistent and one-time tasks that would take place with over a thousand modules (malicious files).
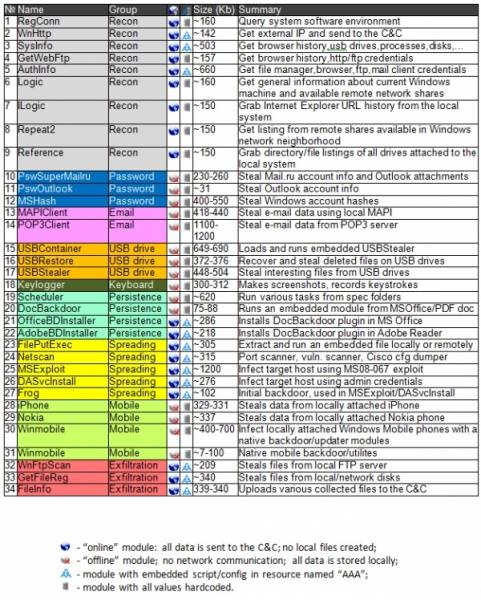
This could include quickly grabbing information from USB drives, recording keystrokes, taking screenshots, retrieving email from Outlook and various mail servers, collecting browsing history and saved passwords, scanning networks to find more potential victims and much more. Who knows what the end goal of this was, but this information could easily be on the black market.
What I don't understand is Kaspersky found this, what the hell were the NSA, CIA, DHS and other various government agencies doing? They all had no idea their networks were infiltrated? I find this very hard to believe.

