More proof of cyber espionage has surfaced with the discovery of miniFlame, a virus that is small and highly flexible. miniFlame is designed to control systems and steal data and was originally discovered in July 2012. When first discovered, it was thought that the virus was simply a module for the Flame virus.
However, further analysis has shown that the "module" is actually an "interoperable tool that could be used as an independent malicious program, or concurrently as plug-in for both the Flame and Gauss malware." Kaspersky research suggests that there were several versions built during 2010 and 2011, some of which are still on infected machines.
The main findings:
- miniFlame, also known as SPE, is based on the same architectural platform as Flame. It can function as its own independent cyber espionage program or as a component inside both Flame and Gauss.
- The cyber espionage tool operates as a backdoor designed for data theft and direct access to infected systems.
- Development of miniFlame might have started as early as 2007 and continued until the end of 2011. Many variations are presumed to be created. To date, Kaspersky Lab has identified six of these variants, covering two major generations: 4.x and 5.x.
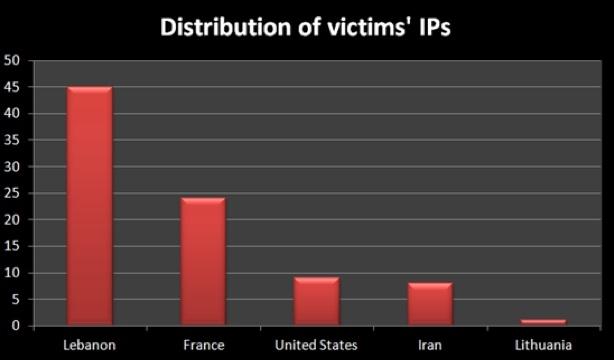
- Unlike Flame or Gauss, which had high number of infections, the amount of infections for miniFlame is much smaller. According to Kaspersky Lab's data, the number of infections is between 10-20 machines. The total number of infections worldwide is estimated at 50-60.
- The number of infections combined with miniFlame's info-stealing features and flexible design indicate it was used for extremely targeted cyber-espionage operations, and was most likely deployed inside machines that were already infected by Flame or Gauss.
Alexander Gostev, Chief Security Expert, Kaspersky Lab, commented: "miniFlame is a high precision attack tool. Most likely it is a targeted cyberweapon used in what can be defined as the second wave of a cyberattack. First, Flame or Gauss are used to infect as many victims as possible to collect large quantities of information. After data is collected and reviewed, a potentially interesting victim is defined and identified, and miniFlame is installed in order to conduct more in-depth surveillance and cyber-espionage. The discovery of miniFlame also gives us additional evidence of the cooperation between the creators of the most notable malicious programs used for cyber warfare operations: Stuxnet, Duqu, Flame and Gauss."
