Save big on the GEEKOM A7 Mini PC with a powerful AMD Ryzen 7000 series processor!
GEEKOM has another incredible deal for TweakTown readers, this time for its GEEKOM A7 Mini PC Ryzen 7000. Powered by the AMD Ryzen R9-7940HS processor, it features RDNA 3 AMD Radeon 780M Graphics to deliver blistering fast 120+ FPS frame rates for games like League of Legends, Counter-Strike, and DOTA 2.
It also has 32GB of dual-channel DDR5 5600 MHz memory, 2TB of PCIe Gen4 SSD storage, Bluetooth 5.2, and Wi-Fi 6E wireless technologies. All this is in a slim, compact form factor measuring 112.4 x 112.4 x 37 mm, or 0.47L, to deliver exceptional speed and performance - small enough to carry around in your pocket!
The GEEKOM A7 Mini PC Ryzen 7000 normally retails for $849, but right now, it's just $649! Enter the coupon code tweaktownA7off (also available for UK customers) at checkout to save a massive $200 on this exceptional Mini PC.
BioMatrix introduces PoY, the world's first UBI token with 60 years Issuance Commitment
Entering the digital future, I have had the chance to explore BioMatrix's cutting-edge blockchain platform. As a technology enthusiast, the idea of the Proof of You (PoY) token caught my attention at first, especially with its pledge to "distribute wealth in a fair and equitable manner."
The selling point of the PoY token is that it is not just a digital asset, but it is an integral part of the company's Universal Basic Income (UBI) distribution strategy, which is designed to connect the user's biological identity to blockchain technology - an important development that could help bridge financial divides around the world.
At its recent launch in Dubai, the BioMatrix platform showcased its potential to redefine the UBI landscape. Like many other secure platforms, BioMatrix is built with user empowerment in mind, and leverages advanced AI and blockchain technology to facilitate its ecosystem growth and expansion. However, the key difference that sets BioMatrix apart from other UBI platforms is using newer cryptography solutions like Zero-Knowledge Proofs (ZKP) to protect user privacy and security.
Unreal Engine 5.4 brings significant updates to ray tracing and rendering for 60 FPS gaming
Although it's an update aimed at game developers, 3D artists, and other creators who use Unreal Engine, the latest Unreal Engine 5.4 update is chock full of good news for gamers across PC, PlayStation, and Xbox, especially for games that will fully utilize Unreal Engine 5's ray tracing and Nanite rendering capabilities.
Many of the updates and improvements are based on developers targeting 60 FPS, and this performance level is becoming the new norm for gamers. "With many developers targeting 60 Hz experiences, we've invested significant effort into improving rendering performance in UE 5.4," Epic writes.
This includes software variable rate shading (VRS) via Nanite, which will bring "substantial performance gains" to rendering while improving hardware ray-tracing (GPU instance culling has been added) and path-tracing performance. The update notes that ray tracing performance is sometimes improved by a factor of 2X.
SK hynix plans $14.6 billion on new chip fab in South Korea to meet 'soaring demand' of HBM
SK hynix has pledged another 20 trillion won (around $14.6 billion USD or so) in preemptively responding to "soaring demand" for HBM memory, which is a key part of AI GPUs.
The South Korean memory giant plans to complete the construction of its new fab in November 2025. Geared up and ready for early mass production, the fab will make major investments in enhancing AI memory market leadership and contributing to the domestic economy in South Korea.
SK hynix's board of directors has approved the plan, which will see the company building the new M15X fab in Cheongju, North Chungcheong Province, for a new DRAM production base, with an investment of around 5.3 trillion won (around $3.9 billion USD or so) for fab construction.
You can pick up AMD's flagship RDNA 3 GPU, the Radeon RX 7900 XTX, for $850
A flagship GPU rarely gets a significant price cut; when you get to the absolute high-end, the high-end performance drives interest, with price coming in second. Just look at NVIDIA's GeForce RTX 4090. It's an absolute monster of a GPU, but it is selling for around $100 - $200 more than its eye-watering $1,599 USD MSRP. And it's a popular option for PC gamers, according to the latest Steam Hardware Survey.
AMD's RDNA 3 flagship, the Radeon RX 7900 XTX, doesn't compete with the GeForce RTX 4090. Its closest NVIDIA counterpart is the GeForce RTX 4080 SUPER, released earlier this year. As the flagship RDNA 3 card with 24GB of GDDR6 memory and decent second-generation ray-tracing performance, it's still very much a 4K powerhouse for PC gaming.
This is why being able to pick one up for $849.99 is a great deal for PC gaming enthusiasts. Granted, this is limited to a single model, the PowerColor Hellhound Radeon RX 7900 XTX, and a single retailer - Newegg. Members can get $100 off the regular $949.99 for a limited time by entering a code at checkout.
Tesla unveils new Model 3 Performance: 0-60 mph in 2.9 seconds, 163 mph top speed
Tesla has just unveiled its new Model 3 Performance electric vehicle, with the company teasing a highly differentiated performance trip that uses Tesla's latest manufacturing and engineering capabilities to create what the company considers to be a "perfect, high-performance daily driver". Check it out:
The new Model 3 Perf ormance features Tesla's very latest Noise, Vibration, and Harshness (NVH) and comfort improvements of the new Model 3, as well as the bespoke chassis hardware the increases performance and stiffness while reducing mass, including adaptive dampers with hollow damper piston rods, multi-sectioned stabilizer bar, ultra-high strength steel springs, and stiffer suspension top mounts.
Tesla bakes in its latest-generation performance drive unit -- the Performance 4DU -- which unlocks even more torque, power, and improved efficiency of the new Model 3 Performance. Compared to the previous Model 3 Performance drive unit, the new Performance 4DU can delivery over 22% more continuous power, over 32% more peak power, and over 16% more peak torque delivery.
GIGABYTE confirms AMD Ryzen 9000 Series processors are coming soon
AMD will most likely announce its new line of Zen 5 desktop processors at Computex 2024 - and now we can confirm that the line-up will be called the AMD Ryzen 9000 Series thanks to GIGABYTE.
In preparation for AMD's not officially confirmed or announced next-gen Ryzen CPU launch, the big AM5 motherboard makers have started releasing BIOS updates to support future or next-gen Ryzen CPUs. Joining companies like MSI and ASUS, GIGABYTE has released an 'AM5 Next Gen' BIOS update for its GIGABYTE AM5 X670, B650, and A620 motherboards.
The announcement makes it very clear what this is for, stating that the update brings support "for the coming AMD Ryzen 9000 Series" of processors. It doesn't get any more clear-cut than that. Zen 5 is coming very soon, and the desktop line-up will be called the Ryzen 9000 Series.
Continue reading: GIGABYTE confirms AMD Ryzen 9000 Series processors are coming soon (full post)
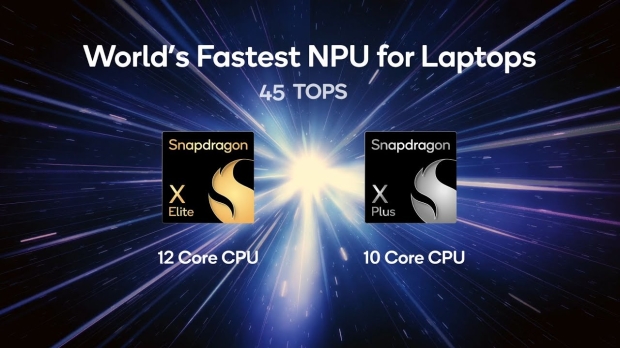
Qualcomm details its Snapdragon X Elite: all SKUs have NPU with 45 TOPS for AI workloads
Qualcomm has been trying for many, many years now to get its Windows on Arm chips up to scratch -- with very, very mixed results -- and now we're being introduced to the new Snapdragon X Elite, which Qualcomm calls the "world's fastest NPU for laptops".
The new Snapdragon X Elite laptop chip has the Qualcomm AI Engine with integrated Qualcomm Hexagon NPU (Neural Processing Unit) with 45 TOPS of AI workload performance. In comparison, Intel's current-gen Core Ultra "Meteor Lake" CPUs top out with 10 TOPS (pun not intended, but it works so well here), while AMD's new Ryzen 8040 "Hawk Point" APUs have 16 TOPS of AI performance.
Qualcomm's new Snapdragon X Elite chip has 75 TOPS of AI performance across the CPU + GPU + NPU and micro NPU, while it's made on the 4nm process by TSMC. On the CPU side of things, we've got the Arm-baed Oryon CPU with 12 cores on the Snapdragon X Elite, or 10 cores on the Snapdragon X Plus.
There's a capsule toy machine in Japan that spits out Intel Core i7-8700 CPUs for around $3
Capsule toy vending machines, or 'gacha' machines, can be found all over Japan. They dispense random toys and collectibles for a small fee, with themed machines covering everything from popular anime franchises to Hello Kitty to stuff as simple and pure as dinosaur toys. Now, we can add Intel CPUs to the list, as someone has spotted a capsule toy machine in Japan that dispenses random Intel CPUs.
Over on X, user @LaurieWired posted a link and YouTube clip from Sawara-San (which is in Japanese) showing that they managed to snag an Intel Core i7-8700 CPU for just 500 Yen (which is around $3 USD) from this CPU Gacha machine. The machine is located outside 1's PC, a store that sells new and second-hand PC parts and things like cameras.
The Intel Core i7 8700 is not that old, with the eighth-generation Coffee Lake from 2018 closely matching the performance of the flagship Intel Core i7 8700K. It's old by 2024 standards for mid-range CPUs, but for around $3, it's a bargain. It's a 6-core 12-thread CPU with a 4.7 GHz Boost Clock - not too shabby. Except, this random 'gacha' version ran into issues.
NVIDIA is helping Japan build their bleeding-edge ABCI-Q quantum supercomputer with HPC and AI
NVIDIA has announced that Japan's new quantum supercomputer will be powered by NVIDIA platforms for accelerated and quantum computing.
Japan's National Institute of Advanced Industrial Science and Technology (AIST) is building a hybrid cloud system of quantum computers and supercomputers called ABCI-Q. Quantum computers are still capable of making a lot of errors if they're operating solo, with supercomputers needing to solve the mistakes and make those complex operations smoother.
NVIDIA is providing the AI GPUs for the new ABCI-Q quantum supercomputer and quantum computing software through its cloud service. NVIDIA will provide over 2000 of its H100 AI GPUs in 500+ nodes interconnected by NVIDIA Quantum-2 InfiniBand, the world's only fully offloadable, in-networking computing platform.
TSMC doesn't need ASML's new High-NA EUV lithography machines for its next-gen A16 process
TSMC has said that its new chip manufacturing technology -- A16 -- will enter production in the second half of 2026, where it will be in a semiconductor battle with Intel for the world's fastest chips.
During a news conference in Santa Clara, California, on Wednesday, Taiwan Semiconductor Manufacturing Company (TSMC) executives said that AI chip makers will be the first adopters of its new A16 process technology rather than smartphone makers like Apple.
Intel came out banging its chest in February this year, saying that with its new High-NA EUV lithography machines from ASML, the company would make the world's fastest chips in the coming years with its new Intel 14A process node. TSMC's senior vice president of business development, Kevin Zhang, told reporters that TSMC has developed its new A16 process node quicker than expected, thanks to the insatiable demand from AI chip companies like NVIDIA.
Noctua's new NH-L12Sx77 low-profile CPU cooler is perfect for small form-factor SFF PCs
Putting together a small form factor (SFF) gaming PC, or productivity PC, can be a lot of fun, as you can fit some serious hardware inside sleek and stylish cases like the Fractal Design Terra.
As one of the premier brands for high-performance and stylish cooling, Noctua has introduced a new low-profile CPU cooler designed specifically for SFF builds: the Noctua NH-L12Sx77. It's an improved (and taller) version of its acclaimed NH-L12S cooler, offering improved thermal performance and more clearance for RAM modules and motherboard heatsinks.
Like the previous model, it includes a Noctua fan preinstalled underneath the fin stack. The fan blows upwards, which Noctua describes as "ideal in compact cases that typically have a perforated panel right above the cooler." With that in mind, Noctua says the NH-L12Sx77 is perfect for smaller chassis like the Fractal Design Terra, SilverStone Milo MILO 12, and Louqe RAW S1.