Hacking, Security & Privacy News - Page 10
President Trump brings ban hammer down on TikTok, WeChat in the US
The Trump administration is bringing down the ban hammer on both TikTok and WeChat in the United States, starting this Sunday.
WeChat will be blocked from US app stores starting on Sunday, with the same bans hitting TikTok on November 12. Commerce Secretary Wilbur Russ explained in a statement: "Today's actions prove once again that President Trump will do everything in his power to guarantee our national security and protect Americans from the threats of the Chinese Communist Party".
President Trump signed an executive order on August 6, giving TikTok 45 days to GTFO of the United States -- well, Sunday is 45 days from August 6.
Continue reading: President Trump brings ban hammer down on TikTok, WeChat in the US (full post)
Joe Biden's official app had a bug that exposed user voting history
If you didn't know, Joe Biden has an official 2020 Presidential campaign app called 'Vote Joe', and unfortunately, it was discovered that the app had a critical bug that exposed user information.
According to a new report from The App Analyst, the app, which is designed to send users pro-Biden texts, nearby events, campaign updates, etc, was found to have a critical bug in it that exposed sensitive user information. The sensitive user information that was exposed was home addresses, birthdays, phone numbers, and prior voting history.
The App Analyst explains that the bug in the app made it very easy for anyone to access this information and that anyone who signed up to the app with a fake email address was granted access to a TargetSmart database. Through this database, users would be able to access more than 190 million voter records. Last week the Biden campaign notified of this bug and has since worked with its third-part app developer to resolve the issue.
Continue reading: Joe Biden's official app had a bug that exposed user voting history (full post)
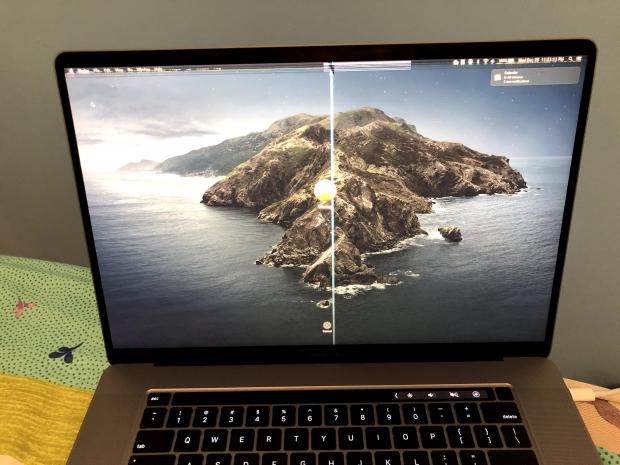
Apple doesn't want you covering up the camera on your MacBook
Apple is warning customers to not cover their camera over concerns of their privacy, as it may damage the MacBook notebook they're using.
The company is telling people not to cover their cameras up as it will also create issues with the automatic brightness and True Tone technologies, with the company explaining: "If you close your Mac notebook with a camera cover installed, you might damage your display because the clearance between the display and keyboard is designed to very tight tolerances".
Apple continues: "Covering the built-in camera might also interfere with the ambient light sensor and prevent features like automatic brightness and True Tone from working. As an alternative to a camera cover, use the camera indicator light to determine if your camera is active, and decide which apps can use your camera in System Preferences".
Continue reading: Apple doesn't want you covering up the camera on your MacBook (full post)
Hacker selling details of 142 million MGM hotel guests on dark web
Remember the MGM Hotel data breach in 2019? It was meant to be 10.6 million people, but it exposed a huge 142 million hotel guests.
Back in February 2020, a data breach affected 10.6 million hotel customers that stayed at MGM Resorts. At the time, the company said that the hackers bnreached their dfatabase in 2019, and that they'd notified people. Well, MGM might have notified a significant lower number of people affected because the numbers are baffling.
ZDNet is reporting that it wasn't 10.6 million customers that had their data breached, but rather over 10x that amount with 142 million customers details now hanging out on the dark web with a hacker selling them for $2939.
Continue reading: Hacker selling details of 142 million MGM hotel guests on dark web (full post)
President Trump exposed to security vulnerability through his own app
As Trump begins to get back out and rally his supporters for this years election, cybersecurity analysts have noticed some security vulnerabilities with the President's official campaign app.
If you are wondering what this official campaign app is, it's an app developed specifically for President Trump's reelection campaign. If you head over to this website, and enter your phone number, you will receive a one time SMS to download the free app that will give you exclusive content and campaign updates. It's available on both the App Store and Google Play.
The issue with this app is that cybersecurity analysts, Noam Rotem and Ran Locar, have found some critical security vulnerabilities in the app. According to WebsitePlanet, where the analysts posted their findings, the app's code "revealed keys and secrets, similar to usernames and passwords, that gave access to different parts of the app, such as its Twitter API." The cybersecurity researchers also said, "While the exposed keys allowed access to many parts of the app, we concluded in our investigation that user accounts remained inaccessible through this vulnerability."
Continue reading: President Trump exposed to security vulnerability through his own app (full post)
Anonymous releases video threatening to expose Minneapolis Police
Anonymous seems to have awoken once again, and this time the hacktivist group is targeting the main source of controversy, the Minneapolis Police Department.
In a video released onto the official Anonymous Twitter account, we see a member of the group wearing the iconic Guy Fawkes mask, talking directly into the camera. The member explains that officers who believe they can kill people and commit other crimes need to be held accountable "just like the rest of us", otherwise they will think they have a license to do whatever they want.
The video goes onto say that the people have "had enough of this corruption and violence from an organization that promises to keep them safe". Anonymous then begins to target the Minneapolis Police Department by saying that the officers behind the George Floyd killing need to face charges, and officer Chauvin should face murder charges. "Unfortunately, we do not trust your corrupted organization to carry out justice, so we will be exposing your many crimes to the world".
Continue reading: Anonymous releases video threatening to expose Minneapolis Police (full post)
This new cyberattack steals data through your power supply
It seems like something out of a Mission: Impossible movie, but a new hack is able to steal data from your PC through your power supply -- yeah, I just said your power supply. Check it out:
The new hack is capable of taking data from a completely air-gapped system, which is completely disconnected from the internet. This means it has no connection to the internet, Wi-Fi, Bluetooth, or any other connection to the internet. Air-gapped systems are considered virtually impossible to siphon data from, but someone is now doing through power supplies.
Dr. Mordechai Guri from the Ben Girion University in Israel is behind the revelations, with a new hack he calls POWER-SUPPLaY. How does it work? Get this: malware is installed onto the target PC, which then reads out the system data and makes some changes to the CPU workload.
Continue reading: This new cyberattack steals data through your power supply (full post)
Coronavirus: Australian government to use smartphones to track people
The Australian government is tightening things Down Under to control coronavirus spread in the country, with lockdowns and borders heavily enforced the Australian government and authorities.
Just like the current app deployment in Singapore, the Australian government is now forging through with plans to release an app to track coronavirus victims, and just exactly where they go. Australia is wanting to lift COVID-19 restrictions that have seen millions of people stop their lives -- work, running businesses, school and everything in between -- and this app, could be the solution.
The Australian government first said that it would be making the coronavirus tracking app mandatory -- but Australian government quickly hopped back a step or two. Australians saw the move as draconian, but Australian Prime Minister Scott Morrison tweeted out that it wouldn't be mandatory.
Continue reading: Coronavirus: Australian government to use smartphones to track people (full post)
You can buy 500,000 Zoom accounts for less than 1c on the dark web
With all of the current shelter-in-place, quarantines, and global lockdowns -- services like Zoom have seen a gigantic surge in popularity and use by companies and people around the world.
Well, did you know that over 500,000 Zoom accounts are being sold on the dark web and hacker forums for as low as 1c each, and in some cases, they're even free? Yeah, so new reports show that Zoom login details are happening through credential stuffing attacks, where hackers will login to Zoom accounts using leaked data from previous breaches.
If the login in successful, that Zoom account login goes into a list and is then sold to other hackers. Some of the Zoom accounts are offered up on a platter on the cheap, or for free -- where other hackers will use them for "zoom-bombing pranks" and "other malicious activities", reports BleepingComputer.
Continue reading: You can buy 500,000 Zoom accounts for less than 1c on the dark web (full post)
Zoom admits data was 'mistakenly' routed through China
Zoom is in serious doo-doo right now, with the videop conferencing provider now admitting that users' calls from around the world were routed through China.
Zoom CEO Eric Yuan admitted that his company "mistakenly" routed calls through China, he explained: "In our urgency to come to the aid of people around the world during this unprecedented pandemic, we added server capacity and deployed it quickly - starting in China, where the outbreak began".
Yuan continued: "In that process, we failed to fully implement our usual geo-fencing best practices. As a result, it is possible certain meetings were allowed to connect to systems in China, where they should not have been able to connect".
Continue reading: Zoom admits data was 'mistakenly' routed through China (full post)