Sonos readies its AirPods Max competitor as FCC approval arrives ahead of launch
Rumors of smart speaker company Sonos entering the headphone market have been floating around for a while now, but so far nothing has actually launched. There was a report last month that Sonos was struggling with a software issue which meant that the launch of the headphones had been pushed until June. The issue was thought to relate to the way the headphones would connect to a user's Wi-Fi network, but now there's a hint that things might be progressing well.
That's after it was discovered by one Reddit user - and then picked up by MacRumors - that the headphones appear to have wound their way through the FCC approval process in the United States, a fact that suggests a launch is edging ever closer.
The headphones themselves are going to work with Bluetooth 2.4GHz as well as WiFI over the 2.4GHz and 5GHz networks as confirmed by the FCC documentation. We expect the new headphones to be designed to go up against Apple's AirPods Max but be priced slightly lower at around $449 which could give them the edge. The headphones will then be priced around the same level as competing products from Sony and the like, although potentially with a slightly different feature set.
2024 iPad Air and iPad Pro refreshes could finally move the camera for better landscape use
When Apple released the 10th-gen iPad in 2022 it brought with it a big first for the company's tablet lineup. The iPad saw its FaceTime camera move from the top of the device to the side, a switch that meant that the camera was better suited to being used when the iPad was in landscape orientation. Now, a new report claimed that the same switch is coming to Apple's best iPads as well.
Historically iPads have had their camera at the top of the display which meant that it was perfect for use when the tablet was held in portrait. But with more iPads now connected to keyboards that meant that the camera was in the wrong place, causing people on video calls to appear as if they were looking to the side. The 10th-gen iPad fixed that, and now it's claimed that the upcoming OLED iPad Pro and new iPad Air models will follow where the 10th-gen iPad left off.
The rumors of the change coming to the iPad Pro have been around for a while now following the discovery of code found in the iOS 17.4 beta in January suggesting the tablet would go that route, Now, the leaker Instant Digital has posted to Weibo to claim that the same change is coming to the iPad Air in both its 10.9-inch and all-new 12,9-inch display sizes.
New iPhone 16 Pro CAD renders show rumored Capture Button and new layout
We're now roughly halfway through the iPhone 15 and iPhone 15 Pro models' lifecycles which means that we are edging ever closer to the arrival of the iPhone 16 and iPhone 16 Pro devices. We've been seeing leaks related to those iPhones since 2023 and we're pretty confident that they will all be announced in September of this year. Now, a new leak appears to have given us a new glimpse at what the high-end iPhone 16 Pro will look like.
The glimpse comes courtesy of 91Mobiles and what appears to be a leak of CAD renders that show the iPhone 16 Pro in all its glory and from all angles. And these renders appear to match up with leaks that we've seen before including the rumored Capture Button.
The renders show that the Action Button is going to be slightly longer than that used on the iPhone 15 Pro, likely in an attempt to make it easier to press. However, the width of the button looks likely to be slightly more than that of the volume buttons that it will be beside, possibly to help make it easier to differentiate between them when the iPhone is in a pocket.
NVIDIA GeForce Now gets G-Sync and Reflex, so it's 'nearly indistinguishable' from a local PC
NVIDIA has beefed up its GeForce Now streaming service with support for a couple of its key technologies for ensuring a smoother and less laggy gaming experience.
The cloud gaming product now has support for G-Sync, so if your display has it on board, you'll now benefit from its ability to minimize any screen tearing and stuttering.
On top of that, NVIDIA Reflex support is here (when streaming at 60 fps or 120 fps, so those running 240 fps on the Ultimate tier don't get it), which reduces input lag (with supported games). In other words, when you click the mouse to fire your gun, for example, that happens just a touch faster - which can, of course, be the difference between life or death in a competitive shooter.
Your HomePod now learns which music streaming service you prefer after installing this update
Apple's HomePod and HomePod mini have a new software update available that makes the smart speakers capable of learning where you like to listen to your music and then use that information for future listening sessions. The new feature, which is part of the HomePod Software 17.4 update, is available to all HomePod owners.
Previously, HomePod owners could use the Home app on their iPhone, iPad, or Mac to choose which music streaming service would be used when they asked their speaker to play music. Streaming music services like YouTube Music, Pandora, TuneIn, and others were all supported but the process required manual intervention whenever the default service needed to be changed. That's no longer the case as a result of this new software update. Spotify is of course a notable exception here because the Swedish streamer has chosen not to add support for HomePod streaming.
According to the software's release notes, Siri will now learn a user's preferred streaming media services, removing the need to include its name when making the request for music to be played.
Experiencing phantom Apple Watch display taps? The watchOS 10.4 update has a fix for that
Some Apple Watch owners have been complaining of so-called phantom display taps no their Apple Watches for some time now, with people saying that apps have been responding as if they touched the display with their fingers. For those who experienced the issue, the results could be dramatic with calls being placed when they aren't needed, messages sent accidentally, and more. Now, there might be some light at the end of the tunnel for those who have been waiting for Apple to issue a fix.
That fix might be part of the watchOS 10.4 software update that Apple rolled out yesterday with Apple's release notes ecpficially calling out the problem. Apple says that the watchOS 10.4 software update fixes an issue that caused some users to experience what it calls false touches and those suffering with the problem will no doubt hope that Apple is true to its word here.
The watchOS 10.4 software update brings with it a handful of other improvements including a fix for a bug that caused some contacts not to sync to Apple Watches for some users.
Microsoft's Surface launch is on March 21 - and could be where AI really steps up to the plate
Microsoft has revealed that it's holding an online event on March 21 where it'll announce some new AI features for Windows and Copilot, with new (unspecified) Surface devices to boot.
Given that the event is entitled a 'New Era of Work' that certainly hints at some pretty major introductions in the pipeline, and as Windows Latest reports, one of the AI features that's supposedly going to be teased is for Windows 11's Paint app.
As previously rumored, this might be a 'LiveCanvas' feature that's akin to the capability seen in Leonardo.Ai. This allows you to sketch a very rough picture, and an AI will fully realize it (and you can use text prompts to direct the AI further in its image composition).
Helldivers 2 future update will make hardest enemies 'easier to bring down'
Helldivers 2 will soon be tweaked with some much-requested changes since its launch: nerfs to the Chargers, Hulks, Bile Titans, and other heavy-duty enemies that are slaying players left, right, and center.
In a new post on Helldivers 2's official Discord, community manager "Spitz" confirmed the news, Spitz explained: "I can confirm that we're currently looking at changes to the spawn rates and health pools of heavy enemies, and will be attempting to spread them out more to prevent large spikes of tougher mobs appearing at the same time, as well as making them a bit easier to bring down."
The developer added: "In addition, we forgot to mention (oops) that the EAT-17 and Recoilless Rifle no longer suffer from a 50% damage decrease when hitting an armored enemy at a 'glance angle' that deflects the shot. Combined with the upcoming adjustment to health and spawn rates, this should make the larger enemies a bit less common, instead spawning more 'chaff' enemies to support them, and should allow players to bring these enemies down with a single well-placed shot. Hopefully this leads to less instances of endless kiting and players being left without any effective weaponry to kill harder enemies."
V-Color's new RDIMM RAM for AMD Threadripper 7000 series CPUs: 768GB kits START at $4840
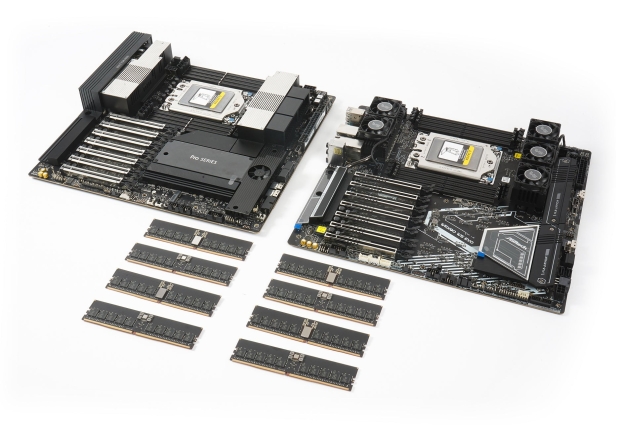
V-color has just unveiled its latest DDR5 OC R-DIMM series memory, which is optimized for AMD's new WRX90 workstation motherboards and CPUs.
The new v-color DDR5 OC R-DIMM has been engineered from the ground up to meet the demand of new AI developers, heavy render modeling, simulation tasks, and high-end performance users. The new series comes with a new technology that targets a known issue with overclocking R-DIMM memory: high temperatures.
To deal with the high temperatures, the new v-color OC R-DIMM for WRX90 features a new micro-heatsink that protects the RCD and PMIC from high temperatures without compromising room for air flow. V-color's new DDR5 OC R-DIMM has been tested with "amazing results" on the ASRock WRX90 WS EVO, ASUS PRO WRX90E-SAGE SE, and Super Micro motherboards.
Helldivers 2's new Warbond is called Cutting Edge: new armor, weapons coming soon
Helldivers 2 developer Arrowhead has teased that its new Warbond, called Cutting Edge, will launch on March 14. It will feature new armor sets, new guns, new capes, new emotes, and so much more. Check it out:
Helldivers 2's new Cutting Edge Warbond will feature three new EX series prototypes: EX-03 Prototype 3, EX-16 Prototype 16, and EX-00 Prototype X. EX-03 Prototype 3 features a rubber underlayer for insulation, with wires operating at a shocking 400,000 volts.
EX-16 Prototype 16 has a warning: electric arcs generate a huge magnetic field, while EX-00 Prototype X is the end result of several billion Super Credits being spent and 12 years of research creating the "Soldier of Tomorrow".