YouTube rolls out safeguards to battle the rise of AI generated video
YouTube has taken to its blog to announce a new rule for its platform designed to protect users from being deceived by creators who are trying to pass off their content as authentic when it was created using the assistance of artificial intelligence-powered tools.
With the unveiling of OpenAI's Sora tool, which is designed to create photorealistic video content from user text prompts, and the popularity of ChatGPT, it isn't a reach to say that AI-powered tools such as Sora will be popular when they are fully developed and released.
Some of the video examples provided by Sora creator OpenAI featured tell-tale signs of AI-powered creation, but the vast majority at a glance, or even viewed by the untrained eye, wouldn't raise alarm bells for synthetic creation, further blurring the line between what's real and what's fake on the internet.
Continue reading: YouTube rolls out safeguards to battle the rise of AI generated video (full post)
Star Wars: Battlefront Classic Collection could be the worst PC and Console release of 2024
It sounded like a slam dunk, taking the beloved multiplayer game series from 2004 and 2005 and bringing it back online in remastered form with support for modern PC hardware and consoles.
Not to be confused with EA and DICE's recent reboot, the original Star Wars Battlefront (2004) and Star Wars Battlefront II (2005) took iconic settings from the original and prequel trilogies and gave them a massively multiplayer Battlefield-style makeover. Although fans have kept these games alive on PC with mods and private servers, they were primed and ready for a comeback.
When news dropped that Aspyr and Lucasfilm Games were releasing a remastered Star Wars Battlefront Classic Collection on March 14, 2024 - with support for up to 64 players - many gamers got their nostalgia glasses ready for a fun trip down memory lane. Except it was anything but.
Fatal Fury City of the Wolves is the first game in the iconic SNK fighting series in 26 years
When you think of the fighting game genre, odds are you're thinking about Street Fighter and Mortal Kombat, two franchises that date back to the early 1990s and are still going strong. Suppose you grew up during that period and spent many afternoons at the local arcade. In that case, there is no doubt you'd be aware of SNK and its iconic output, including series like Fatal Fury, King of Fighters, and Samurai Shodown.
Interestingly, Fatal Fury, the SNK fighting game franchise that began in 1991 (making it one of the oldest fighting games in video game history), hasn't received a new entry since 1999, when Garou: Mark of the Wolves was released.
Fast-forward to 2024, and SNK has announced that Fatal Fury will return in early 2025 after a 26-year absence.
Easy Anti-Cheat responds to Apex Legends pro players being hacked mid-game
In what seems like a first, Apex Legends professional players were hijacked by a hacker during the Apex Legends Global Series to be given cheats, resulting in the NA finals being postponed.
The Apex Legends North American finals were infiltrated by at least two hackers named "Destroyer2009" and "R4andom", who managed to somehow gain access to at least two professional players' PCs during a match. As the match was being streamed to thousands of fans around the world, a message box briefly popped up and then disappeared, which was followed by the player realizing that they had aimbot, wallhacks, and other cheats. Shortly after the discovery, the match was promptly ended.
Following the shutdown of the match Anti-Cheat Police Department, a group of volunteers that specialize in gathering intelligence on cheats to detect and disrupt cheating vendors, took to its X account to provide a public service announcement, stating that an RCE exploit was used to gain access to the players' PCs. For those that don't know, an RCE exploit is a "remote code execution", which means the hackers were able to execute codes on the target machines remotely.
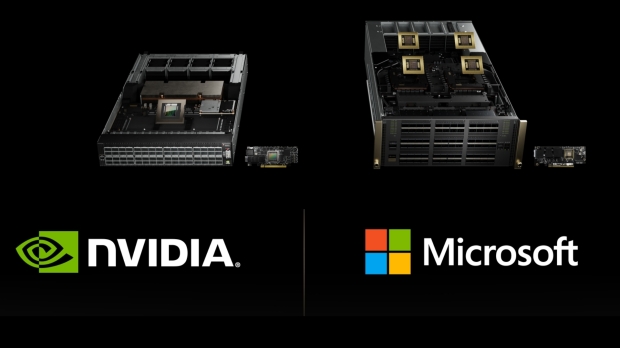
OpenAI, Microsoft, Amazon, Meta, Google, Tesla, and more are all on the NVIDIA Blackwell train
NVIDIA has unveiled its next-gen Blackwell AI GPU, which features 208 billion transistors, 192GB of super-fast HBM3E memory, a cutting-edge custom TSMC 4NP process, and groundbreaking new networking that sees NVIDIA NVLink deliver 1.8TB/s bidirectional throughput per GPU.
The company also announced its new NVIDIA GB200 Grace Blackwell Superchip, which connects two NVIDIA B200 Tensor Core GPUs to the NVIDIA Grace CPU "over a 900GB/s ultra-low-power NVLink chip-to-chip interconnect." With serious AI horsepower, NVIDIA's powerful next-gen AI hardware arrives during the AI boom, so, unsurprisingly, it announced its long list of Blackwell partners.
NVIDIA writes, "Among the many organizations expected to adopt Blackwell are Amazon Web Services, Dell Technologies, Google, Meta, Microsoft, OpenAI, Oracle, Tesla, and xAI." Even though most, if not all, of these companies are investing in creating their own AI chips and hardware for generative AI-which is used in everything from scientific research to medicine and chatbots-Blackwell will drive many of the advances over the next few years.
Microsoft and NVIDIA to integrate generative AI and Omniverse tech in Azure and Microsoft 365
It's been a massive day for AI news, with NVIDIA's premiere GTC 2024 AI conference underway. Earlier today, the company unveiled its next-gen Blackwell AI GPU - an unprecedented AI monster with 208 billion transistors and 192GB of super-fast HBM3E memory.
NVIDIA's first multi-GPU die is built on a cutting-edge TSMC 4NP process. It allows organizations to run real-time generative AI on "trillion-parameter large language models" at up to 25X less cost and energy consumption than its Hopper predecessor. Throw in the latest version of NVIDIA NVLink that delivers 1.8TB/s bidirectional throughput per GPU, and it's no wonder everyone is signing up to join the Blackwell family - including Microsoft.
Alongside the big Blackwell reveal, NVIDIA and Microsoft have announced that Microsoft Azure will adopt NVIDIA Grace Blackwell Superchips to help accelerate customer and first-party (Microsoft's own) AI offerings, Including Microsoft 365, aka the online versions of Microsoft Word, PowerPoint, Excel, and OneNote. NVIDIA GPUs and NVIDIA Triton Inference Server will help power Microsoft Copilot for Microsoft 365.
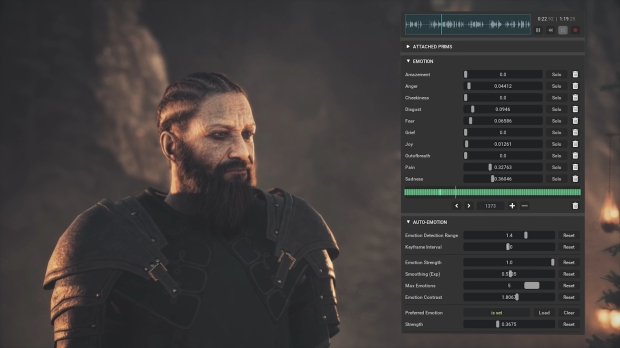
NVIDIA Audio2Face uses AI to generate lip synching and facial animation, showcased in two games
Localization is a big thing in gaming, where a game's dialogue and presentation are recorded in various languages to reach a global audience. Like how Netflix dubs all of its original programming into multiple languages, localization for games is a complex process that requires accurately translating dialogue and text, maintaining dramatic or comedic tones, and then re-recording dialogue with voice actors from different countries.
Where games differ from movies or television drama is that all performances are digital and completely malleable, which is why you've got a situation where Sony's PlayStation-exclusive Ghost of Tsushima (which is coming soon to PC) offers both English and native Japanese language options with full lip-syncing and correct facial animation.
Although it's possible to do this for dozens of languages, Ghost of Tsushima limits full lip-synching to two language options due to the task's complexity and the animation involved. This is where generative AI, specifically NVIDIA's Audio2Face technology, will step in.
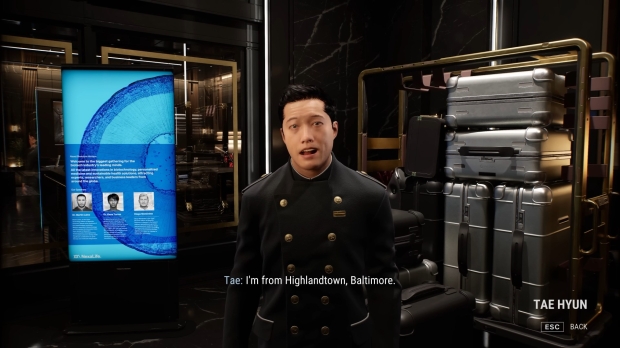
NVIDIA's Covert Protocol tech demo has you become a detective investigating AI Digital Humans
At GDC 2024, NVIDIA presented a new tech demo for a theoretical detective game, Covert Protocol, created in collaboration with Inworld. If you recall NVIDIA's recent AI collabs, which created cyberpunk-style tech demos featuring AI avatars you can interact with, this takes it all one step further. It presents an old-school adventure game where you're talking to characters to solve a mystery in a brand-new way.
In Covert Protocol, you play a private detective and explore a realistic environment, speaking to 'digital humans' as you piece together critical and key information. The game is powered by the Inworld AI Engine, which fully uses NVIDIA ACE (the technology we've been following over the past year) services to ensure that no two playthroughs are the same.
"This level of AI-driven interactivity and player agency opens up new possibilities for emergent gameplay," NVIDIA writes. "Players must think on their feet and adapt their strategies in real-time to navigate the intricacies of the game world."
NVIDIA creates Earth-2 digital twin: generative AI to simulate, visualize weather and climate
NVIDIA isn't just changing up the GPU and AI GPU game with its Blackwell AI GPU chips, announcing Earth-2 today during the GPU Technology Conference (GTC).
NVIDIA announced its new Earth-2 climate digital twin cloud platform so people could simulate and visualize weather and climate at scales never seen before. Earth-2's new cloud APIs are available on NVIDIA DGX Cloud, allowing virtually anyone to create AI-powered emulations to make interactive, high-resolution simulations ranging from the global atmosphere to localized cloud cover all the way through to typhoons and mega-storms.
The new Earth-2 APIs offer AI models that use new NVIDIA generative AI model technology called CorrDiff, using state-of-the-art diffusion modeling, capable of generating 12.5x higher resolution images than current numerical models that are 1000x faster and 3000x more energy efficient.
Honor reveals the first laptop with 24GB RAM, also packs Intel Core Ultra 'Meteor Lake' CPU
It looks like Honor is the first to market with a new laptop featuring 24GB of DDR5 memory, with its new MagicBook Pro 16 AI laptop teased on Geekbench. Check it out:
The new Honor MagicBook Pro 16 AI laptop features 24GB of LPDDR5X memory, versus the usual SO-DIMM memory modules. Inside, there are 8 individual memory chips, each packing 3GB for a total of 24GB of LPDDR5X-6400 memory. This is great to see, as 24GB of RAM is a fantastic step up from 16GB, and while it's not quite 32GB, it's once again, not 16GB. Great stuff.
We should see 12GB SO-DIMM memory modules in the near future, which will allow for up to 48GB of DDR5 memory as long as the laptop of choice has four DIMM slots, of course.