Intel is 'wooing' TSMC's market supply chain to help its own foundry business
Intel is well aware that it faces multiple obstacles in its course to becoming the biggest in the semiconductor foundry industry; where we're hearing Intel is talking to Taiwan-based factories that have worked with TSMC, to help its Intel Foundry business.
In a new report from DigiTimes, the outlet says that the strength of Intel's R&D power shouldn't be underestimated. The R&D technology -- including ASML's bleeding-edge EUV lithography machine delivered to its US operations at the cost of $380 million and split into a new Intel Foundry business -- is as good as and even ahead of TSMC with some of its revolutionary, innovative technologies.
The hurdles that Intel faces are a few: companies don't have the same trust in Intel to fab their chips as they do with TSMC, with high manufacturing costs, yield rates, efficiency, and on-schedule in terms of mass production aren't close to what TSMC is, and has been capable of over the years.
Google announces Arm-based CPU for AI called Axion, 50% more performance than current-gen x86
With all the big tech companies investing billions in AI data centers, research, and the creation of generative AI models and tools, many are looking to create their own hardware as an alternative to NVIDIA's chips - while competing with AMD, Intel, and new AI-chip players like Microsoft.
Google is entering the race with its own arm-based processor designed for the AI market. Like Google's tensor processing units (TPUs), which developers can access only via Google Cloud, the Arm-based CPU called Axiom will apparently deliver "superior performance to x86 chips."
How much extra performance? According to Google, Axiom offers 30% better performance than "general purpose Arm chips" and 50% better performance than "current generation x86 chips" as produced by Intel and AMD.
Blizzard games are returning to China thanks to a new deal with long-time partner NetEase
Blizzard games like World of Warcraft and Diablo have been prominent in China for several years, thanks to a deal made with local publishing and gaming giant NetEase to bring its popular games and franchises to the country. However, the deal between the two expired in 2023, with Blizzard and NetEase pointing the finger at each other - citing the other party as the reason for the agreement not being renewed.
It got so heated that NetEase employees tore down a World of Warcraft statue at its offices, with both companies suing each other. Well, it looks like time heals all wounds - or a change in management does. With Microsoft now in charge of Activision Blizzard and its properties, a new deal has been struck to bring Blizzard Entertainment games like Warcraft, StarCraft, and Diablo back to China this summer.
As part of the new deal, both parties have also agreed to explore bringing NetEase titles to Microsoft Xbox and other gaming platforms in the West.
Meta's next-gen in-house AI chip is made on TSMC's 5nm process, with LPDDR5 RAM, not HBM
Meta has just teased its next-gen AI chip -- MTIA -- which is an upgrade over its current MTIA v1 chip. The new MTIA chip is made on TSMC's newer 5nm process node, with the original MTIA chip made on 7nm.
The new Meta Training and Inference Accelerator (MTIA) chip is "fundamentally focused on providing the right balance of compute, memory bandwidth, and memory capacity" that will be used for the unique requirements of Meta. We've seen the best AI GPUs on the planet using HBM memory -- with HBM3 used on NVIDIA's Hopper H100 and AMD Instinct MI300 series AI chips -- with Meta using low-power DRAM memory (LPDDR5) instead of server DRAM or LPDDR5 memory.
The social networking giant created its MTIA chip was the company's first-generation AI inference accelerator that the company designed in-house for Meta's AI workload in mind. The company says that their deep learning recommendation models are "improving a variety of experiences across our products".
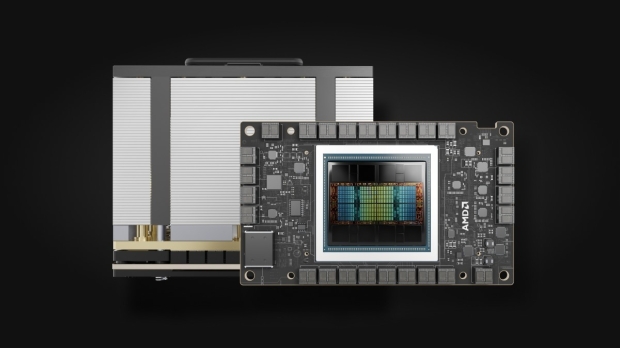
AMD's upgraded Instinct MI350 with newer 4nm node, HBM3E rumored for later this year
AMD has already confirmed it has refreshed variants of its Instinct MI300 series AI and HPC processors in the second half of this year, with a tweaked Instinct MI350X featuring ultra-fast HBM3E memory.
AI GPU competitor NVIDIA has its current Hopper H100 AI GPU with HBM3 memory, while its newly announced H200 AI GPU features ultra-fast HBM3E memory -- the world's first AI GPU with HBM3E memory. The next-gen Blackwell B200 AI GPU ships with ultra-fast HBM3E memory as standard.
Market research firm TrendForce recently teased AMD's new Instinct MI350X. The firm says the new Instinct MI350X will feature chiplets made on TSMC's newer 4nm process node, which is an enhanced version of TSMC's 5nm-class process node. The new TSMC N4 process node will allow AMD to choose between increasing performance or lowering power consumption on its tweaked Instinct MI350X over the MI300 series AI GPU.
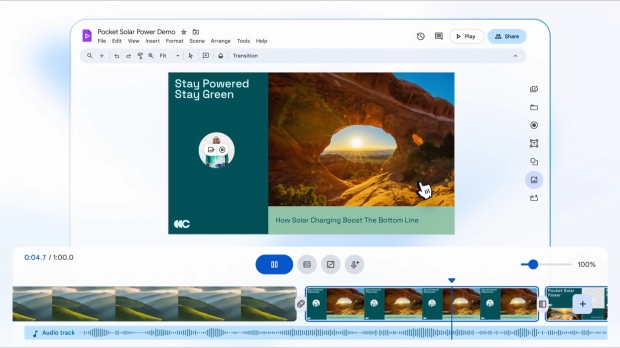
Google Vids is the company's new AI-powered video creation tool for work
Google Vids is the company's latest productivity app. It is part of the Google Workspace productivity suite, which includes Gmail, Docs, Sheets, Slides, Drive, Meet, and more. Per the name, it's all about video, with the Gemini AI-powered tool set to make video editing, creation, and writing a breeze.
As it's part of Google Workspace, one example of how it could be used would be to create a tutorial or sales-focused video using existing Google Docs or Slides. With Gemini, it can generate a script and a short video that users can then edit to change various aspects of the creation. As a tool, it's designed to streamline the video creation process so you can put something together without knowing much, if anything, about video editing.
As a work-centric app, Google Vids is an extension of productivity apps like PowerPoint and Slides - bridging the gap from presentation or pitch to video. As a part of Google Workspace, it can draw assets and data from Google Drive, letting you add voiceover, music, and AI-generated art.
Corsair teams with Yeston for new Vengeance DDR5 RAM that matches Yeston Sakura GPUs
Corsair has teamed with Chinese company Yeston on some new Sakura-themed Vengeance DDR5 memory, check it out:
The new Corsair Vengeance DDR5 memory was spotted on Corsair's China Weibo account, showing off the new DDR5 memory modules with Sakura-themed flowers and anime-inspired characters dressed in beautiful bridal gowns. Each side of the Sakura-themed Vengeance DDR5 memory is styled differently, with one side featuring chibi stylings and the other having a more typical Japanese animation.
Inside, they're regular Corsair Vengeance DDR5 memory that will work with either AMD Ryzen 7000 series "Zen 4" processors or Intel 12th Gen, 13th Gen, and 14th Gen CPUs if you've got the right motherboard ready for DDR5 memory. Corsair's new Sakura-themed Vengeance DDR5 memory seems only available in China for now, but hopefully, they make it across the pond.
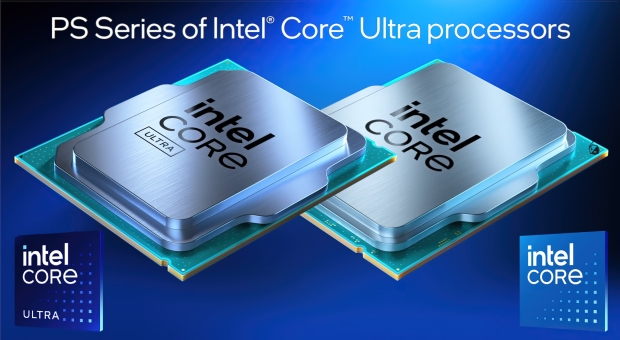
Intel's new Meteor Lake-PS processors: LGA 1851 socket, Arc GPU, NPU for AI for edge computing
Intel has just unveiled a range of new Meteor Lake-PS processors, designed for edge computing, featuring Arc graphics, and an NPU for AI workloads. Intel announced its new Meteor Lake processors on the new LGA 1851 socket at its Vision 2024 event.
The new Meteor Lake-PS processors are aimed at customers in retail, education, industrial, kiosk, and smart point-of-sale systems for brick-and-mortar stores, among others. Edge computing is a gigantic business for Intel, with over 90,000 deployments worldwide.
The new edge-focused Meteor Lake CPUs are the first to debut using the new LGA 1851 socket, which will be used on the next-gen Core Ultra 200 "Arrow Lake-S" processors on the desktop late this year. The company has unveiled 9 new Meteor Lake-PS processors so far, with five of those being Meteor Lake-PS 15W chips, with four Meteor Lake-PS 45W processors.
Intel's next-gen LGA 1851 socket spotted: ready for Arrow Lake-S CPUs later this year
Intel's upcoming LGA 1851 socket has been teased, shown off in the flesh at Embedded World 2024 this week.
Intel introduced new Meteor Lake and Raptor Lake Refresh processors that were designed for socketed systems operating on the edge, which will see the birth of the LGA 1851 socket for Meteor Lake, something that the company had planned, but delayed, and now it's here.
The new LGA 1851 socket will be for both mobile and desktop platforms, where on the desktop side of things we'll have the new Core Ultra 200 "Arrow Lake-S" series processors, while Meteor Lake-PS chips will also use the new LGA 1851 socket. The new LGA 1851 socket was shown on a new motherboard at Embedded World, spotted by our friends at ComputerBase.
Leak suggests AMD Zen 5 CPUs will be called Ryzen 9000
We still aren't sure of what naming scheme AMD might go for with its next-gen Zen 5 processors, but it appears to be the case that Team Red has plumped for Ryzen 9000.
Although we should make it clear that this is far from confirmation, but nonetheless, the sighting of the Ryzen 9000 family, made by leaker HXL on X (formerly Twitter), is a telling one. The Ryzen 9000 name is mentioned in an AMD chipset driver from ASUS.
This was the favorite choice between the potential options bandied about via the rumor mill, which were that AMD could stick with Ryzen 8000, but was more likely to switch to Ryzen 9000 (to make the distinction between the APUs and mobile CPUs already released with the former brand).
Continue reading: Leak suggests AMD Zen 5 CPUs will be called Ryzen 9000 (full post)